Source Link
Brahma Chellaney
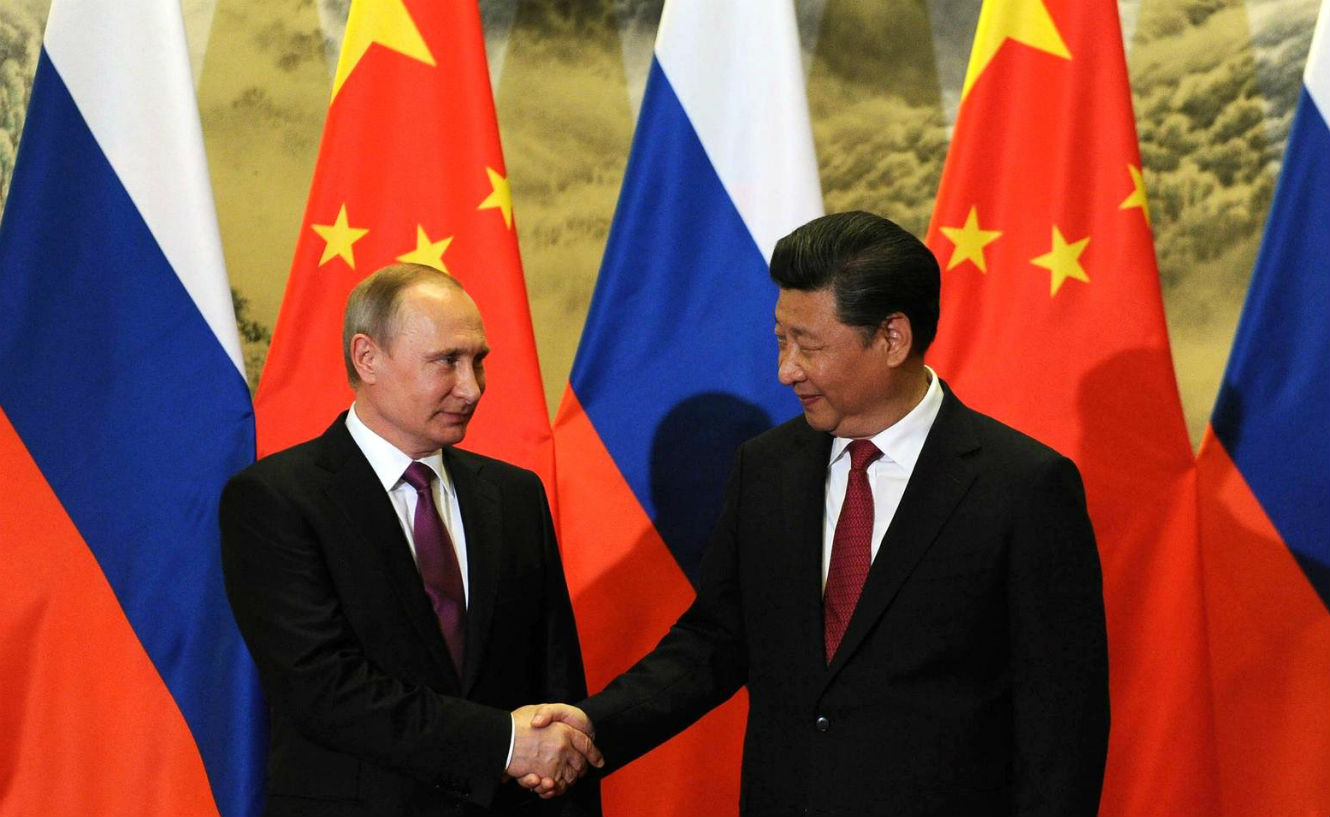
 China is taking steps to ensure that countries will not be able to escape their debts. Photo: Reuters
China is taking steps to ensure that countries will not be able to escape their debts. Photo: Reuters
If there is one thing at which China’s leaders truly excel, it is the use of economic tools to advance their country’s geostrategic interests. Through its $1 trillion “One Belt, One Road” initiative, China is supporting infrastructure projects in strategically located developing countries, often by extending huge loans to their governments. As a result, countries are becoming ensnared in a debt trap that leaves them vulnerable to China’s influence.
Of course, extending loans for infrastructure projects is not inherently bad. But the projects that China is supporting are often intended not to support the local economy, but to facilitate Chinese access to natural resources, or to open the market for low-cost and shoddy Chinese goods. In many cases, China even sends its own construction workers, minimizing the number of local jobs that are created.
Several of the projects that have been completed are now bleeding money. For example, Sri Lanka’s Mattala Rajapaksa International Airport, which opened in 2013 near Hambantota, has been dubbed the world’s emptiest. Likewise, Hambantota’s Magampura Mahinda Rajapaksa Port remains largely idle, as does the multibillion-dollar Gwadar port in Pakistan. For China, however, these projects are operating exactly as needed: Chinese attack submarines have twice docked at Sri Lankan ports, and two Chinese warships were recently pressed into service for Gwadar port security.
In a sense, it is even better for China that the projects don’t do well. After all, the heavier the debt burden on smaller countries, the greater China’s own leverage becomes.
Moreover, some countries, overwhelmed by their debts to China, are being forced to sell to it stakes in Chinese-financed projects or hand over their management to Chinese state-owned firms. In financially risky countries, China now demands majority ownership up front. For example, China clinched a deal with Nepal this month to build another largely Chinese-owned dam there, with its state-run China Three Gorges Corporation taking a 75% stake.
As if that were not enough, China is taking steps to ensure that countries will not be able to escape their debts. In exchange for rescheduling repayment, China is requiring countries to award it contracts for additional projects, thereby making their debt crises interminable. Last October, China cancelled $90 million of Cambodia’s debt, only to secure major new contracts.
Some developing economies are regretting their decision to accept Chinese loans. Protests have erupted over widespread joblessness, purportedly caused by Chinese dumping of goods, which is killing off local manufacturing, and exacerbated by China’s import of workers for its own projects.
New governments in several countries, from Nigeria to Sri Lanka, have ordered investigations into alleged Chinese bribery of the previous leadership.
In retrospect, China’s designs might seem obvious. But the decision by many developing countries to accept Chinese loans was, in many ways, understandable. Neglected by institutional investors, they had major unmet infrastructure needs. So when China showed up, promising benevolent investment and easy credit, they were all in. It became clear only later that China’s real objectives were commercial penetration and strategic leverage; by then, it was too late, and countries were trapped in a vicious cycle.
Sri Lanka is Exhibit A. Though small, the country is strategically located between China’s eastern ports and the Mediterranean. Chinese President Xi Jinping has called it vital to the completion of the maritime Silk Road.
China began investing heavily in Sri Lanka during the quasi-autocratic nine-year rule of President Mahinda Rajapaksa, and China shielded Rajapaksa at the UN from allegations of war crimes. China quickly became Sri Lanka’s leading investor and lender, and its second-largest trading partner, giving it substantial diplomatic leverage.
It was smooth sailing for China, until Rajapaksa was unexpectedly defeated in the early 2015 election by Maithripala Sirisena, who had campaigned on the promise to extricate Sri Lanka from the Chinese debt trap. True to his word, he suspended work on major Chinese projects.
But it was too late: Sri Lanka’s government was already on the brink of default. So, as a Chinese state mouthpiece crowed, Sri Lanka had no choice but “to turn around and embrace China again”. Sirisena, in need of more time to repay old loans, as well as fresh credit, acquiesced to a series of Chinese demands, restarting suspended initiatives, like the $1.4 billion Colombo Port City, and awarding China new projects.
Sirisena also recently agreed to sell an 80% stake in the Hambantota port to China for about $1.1 billion. Now, Rajapaksa is accusing Sirisena of granting China undue concessions.
By integrating its foreign, economic, and security policies, China is advancing its goal of fashioning a hegemonic sphere of trade, communication, transportation, and security links. If states are saddled with onerous levels of debt as a result, their financial woes only aid China’s neocolonial designs. Countries that are not yet ensnared in China’s debt trap should take note—and take whatever steps they can to avoid it.
Brahma Chellaney is professor of strategic studies at the New Delhi-based Centre for Policy Research and fellow at the Robert Bosch Academy in Berlin.
 For the CDS to be effective in the tasks envisaged by the ministry, he would need to have full control on the decision making apparatus.
For the CDS to be effective in the tasks envisaged by the ministry, he would need to have full control on the decision making apparatus.