Steve Prentice
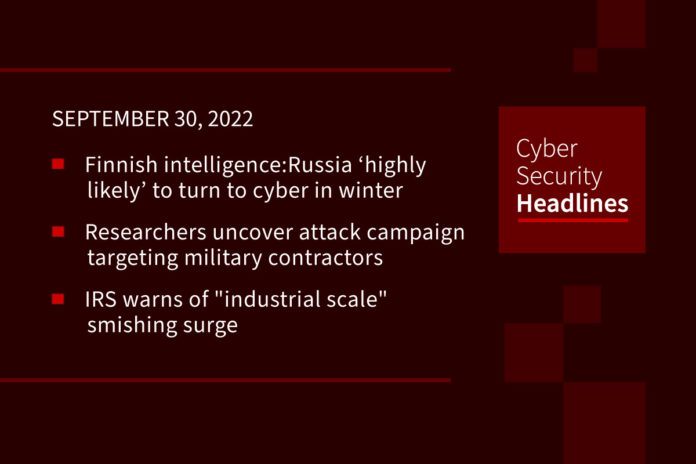
Finnish intelligence warns Russia ‘highly likely’ to turn to cyber in winter
The head of the Finnish Security Intelligence Service (Suojelupoliisi or SUPO) says it is “highly likely that Russia will turn to the cyber environment over the winter” for espionage due to challenges impacting its human intelligence work. In the unclassified National Security Overview 2022 published on Thursday, SUPO said that Russia’s traditional intelligence gathering approach using spies with diplomatic cover “has become substantially more difficult since Russia launched its war of aggression in Ukraine, as many Russian diplomats have been expelled from the West.” SUPO assessed that Russian citizens who occupied critical positions in Finland were particularly at risk of coercion from the Russian authorities.
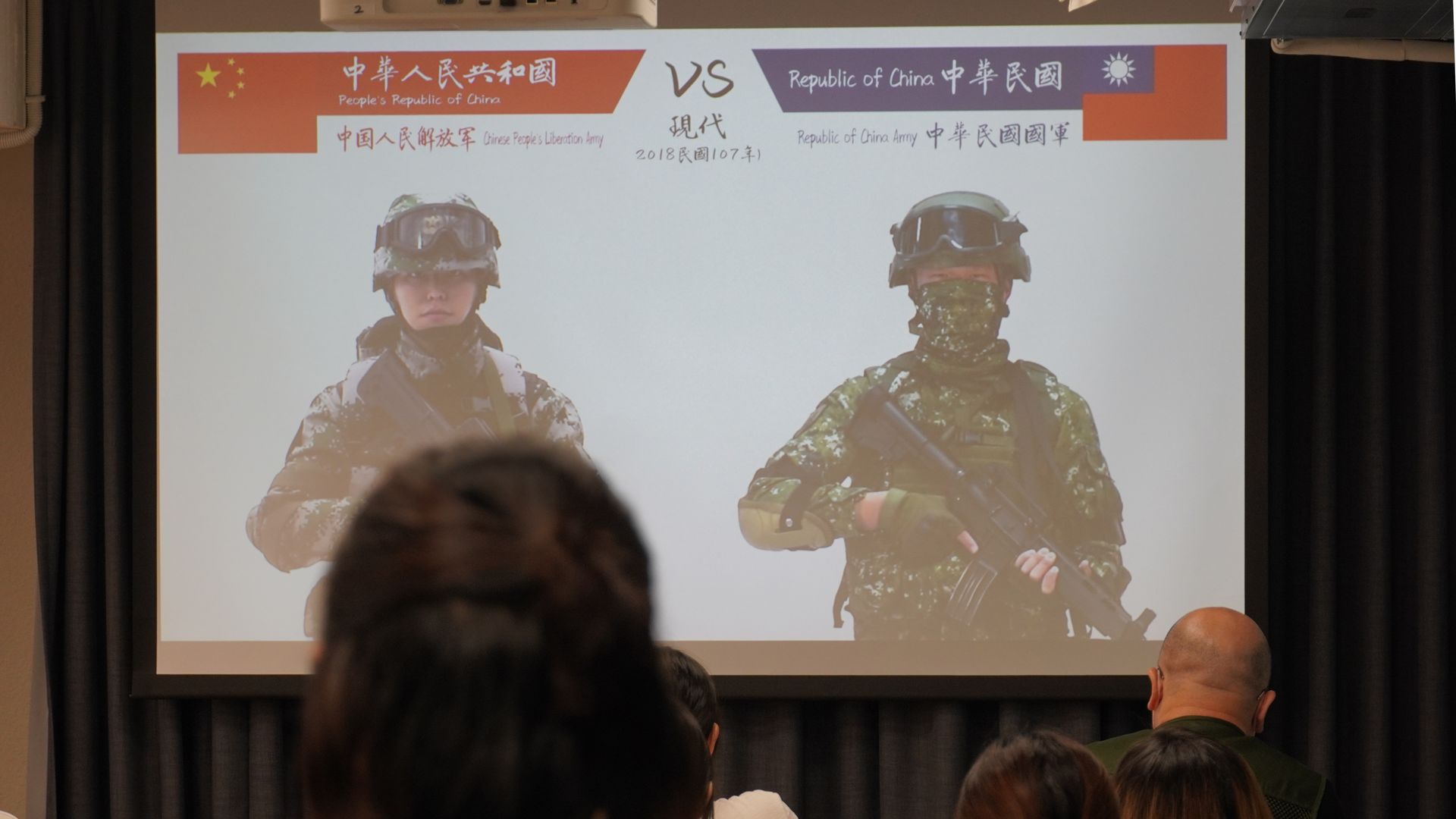
Researchers uncover covert attack campaign targeting military contractors
A new covert attack campaign singled out multiple military and weapons contractor companies with spear-phishing emails to trigger a multi-stage infection process designed to deploy an unknown payload on compromised machines. The highly-targeted intrusions, dubbed STEEP#MAVERICK by Securonix, also targeted a strategic supplier to the F-35 Lightning II fighter aircraft. Starting in late summer 2022 the infection chains begin with a phishing mail with a ZIP archive attachment containing a shortcut file that claims to be a PDF document about “Company & Benefits,” which is then used to retrieve a stager — an initial binary that’s used to download the desired malware — from a remote server.
IRS warns of “industrial scale” smishing surge
In a news alert yesterday, the tax agency said it had identified thousands of fake domains so far in 2022, used to facilitate the so-called “smishing” scams, and designed to steal victims’ personal and financial information. Spoofed to appear as if sent from the IRS, these text messages often use lures like fake COVID relief, tax credits or help setting up an IRS online account, it said. They might request personal information or covertly download malware to the user’s device by tricking them into clicking on a malicious link. “This is phishing on an industrial scale so thousands of people can be at risk of receiving these scam messages,” said IRS commissioner Chuck Rettig.
New malware backdoors VMware ESXi servers to hijack virtual machines
Hackers have found a new method to establish persistence on VMware ESXi hypervisors to control vCenter servers and virtual machines for Windows and Linux while avoiding detection. With the help of malicious vSphere Installation Bundles, an attacker is now able to install two backdoors on the bare-metal hypervisor that researchers have named VirtualPita and VirtualPie. Researchers also uncovered a unique malware sample that they called VirtualGate, which includes a dropper and a payload. This attack requires the threat actor to have admin-level privileges to the hypervisor. While this may appear to lower the risk, adversaries often lurk on the victim network waiting for an opportunity to reach valuable assets or extend their presence.
Can you trust that your content and data is free of malware and ransomware? With Votiro you can. Votiro removes evasive and unknown malware from content in milliseconds, without impacting file fidelity or usability. It even works on password-protected and zipped files. Plus, it’s an API, so it integrates with everything – including Microsoft 365. Learn more at Votiro.com.
UN elects first female tech agency secretary-general
Doreen Bogdan-Martin has become the first woman to be elected as secretary-general of the International Telecommunication Union (ITU), the main technology agency within the UN. Originally founded in 1865 to manage the first international telegraph networks, the ITU now has an important role in facilitating the use of radio, satellite and the internet, including assigning satellite orbits globally, co-ordinating technical standards, and improving infrastructure in the developing world.
Brave browser to start blocking annoying cookie consent banners
Such notifications are incredibly annoying but have become necessary to do business online to comply with data protection regulations like GDPR. In some cases, however, these banners can serve as trackers themselves, as they engage in a privacy-breaching data exchange before the user even has a chance to opt out. Brave will now proactively detect and block the cookie consent banners, removing both a distraction and a potential privacy risk for users. The roll-out of the new system will begin in Brave Nightly 1.45, scheduled for release in October, and will gradually pass to the stable version on Windows and Android. iOS will follow soon afterward.
Privacy advocates want the FTC to take on invasive daycare apps
The Federal Trade Commission should review privacy and security concerns with daycare and early education apps, the Electronic Frontier Foundation urged in a letter to the agency Wednesday. The letter builds on the EFF director of engineering Alexis Hancock’s research, which uncovered a variety of security concerns including the insecure cloud storage of photos of children. Security researchers have found that more than half of the 42 apps they looked at did not disclose the use of third-party trackers. The FTC is tasked with enforcing the Children’s Online Privacy Protection Act, which controls what data companies can collect from children under 13. However, because daycare apps are collecting children’s data directly from parents and daycare providers, those protections have limited application.
Pentagon bug bounty program yields results
Following up on a story we brought you in July, the department’s July bug bounty program, “Hack US,” uncovered 349 were “actionable” reports. Melissa Vice, director of the DoD’s vulnerability disclosure program, said an initial evaluation of the program’s results found that the most commonly identified vulnerability was categorized as “information disclosure.” Other top flaws discovered through the effort included improper access and generic SQL injection.