Pranav Dixit
 Pakistani soldiers stand next to what Pakistan says is the wreckage of an Indian fighter jet shot down in Pakistan-controlled Kashmir on Feb. 28.
Pakistani soldiers stand next to what Pakistan says is the wreckage of an Indian fighter jet shot down in Pakistan-controlled Kashmir on Feb. 28.
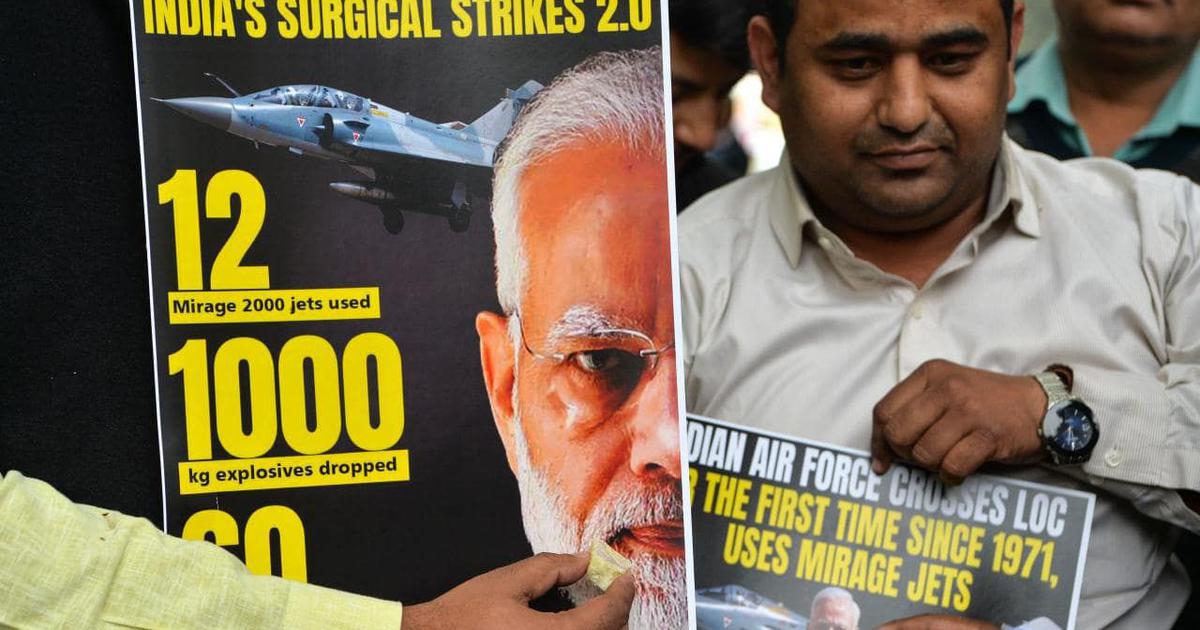
India and Pakistan, both countries that possess over a hundred nuclear warheads each, came close to the brink of war this week. But even as fighter aircraft from both nations invaded each other’s air space, a full-blown misinformation war about the conflict raged on the internet.
“Misinformation has been used to start wars throughout history. It would be foolish to think that our time is the exception to the rule,” Aviv Ovadya, cofounder of the Thoughtful Technology Project, a San Francisco–based nonprofit dedicated to preventing harmful misinformation, told BuzzFeed News.















/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/OH42WCQUFRHTNC5F4JIVKROQBA.jpg)
