Jassem Al Salami on Jul 16
Rocket and drone attacks can swamp anti-missile batteries
On July 7, Palestinian militia group Islamic Jihad launched some 35 small rockets nearly simultaneously at southern Israel—the latest escalation of this summer’s tit-for-tat violence.
The Iron Dome missile battery near Ashkelon could intercept only three of the rockets. Twenty of the projectiles hit populated areas, injuring one person in the city of Sderot.
This was the militants’ master plan—to saturate the Iron Dome with tens or hundreds of cheap munitions. But the Palestinians never assumed the tactic immediately would work. And they knew the Israeli air force would retaliate against the rocketeers.
The Palestinians had back-up plans.
On July 8, the Israeli air force attacked 50 sites in Gaza, largely targeting rocket launchers. The air strikes temporarily suppressed the Palestinians’ short-range ballistic attacks on southern Israel.
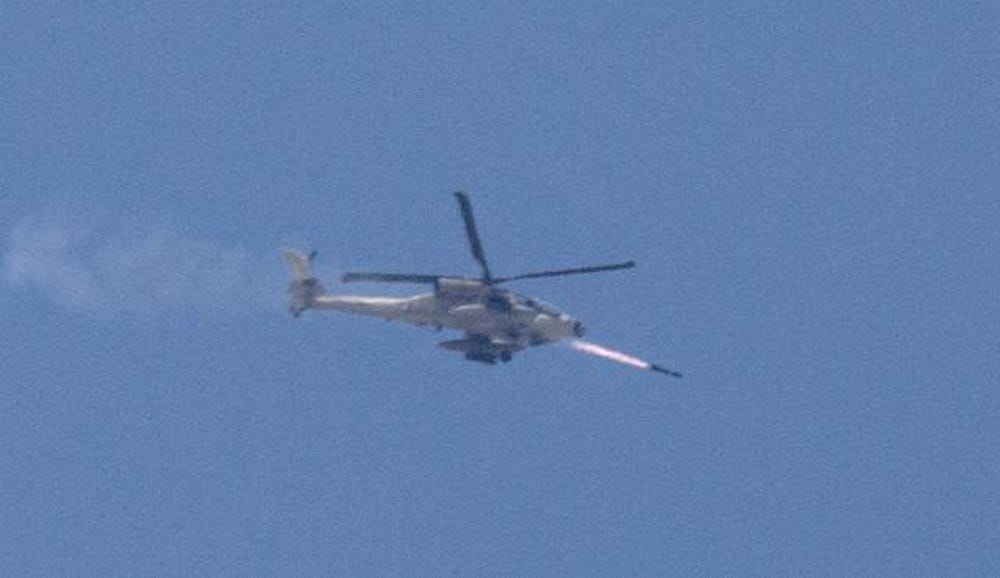
An Israeli Apache helicopter fires a Hellfire missile. Israeli Defense Forces photo
For starters, they switched to targets deeper inside Israel—targets they knew were outside the Iron Dome’s defensive umbrella. They aimed R-160 rockets at Haifa, in northern Israel along the coast.
The R-160 is a modified version of the infamous Fadjr-5 missile with an added booster. The R-160 carries a 450-pound warhead, just like the Fadjr-5, but it can travel 170 kilometers, more than double the range of the Fadjr-5.
But the extra range comes at a cost. The R-160 is wildly inaccurate. All the rockets the Palestinians fired at Haifa fell into unpopulated areas or the sea.
The militants’ next move was to deploy suicide teams in Israel. Not suicidebombers—rather attackers who never expected to survive their assaults. The first special operations teams deployed from the sea on July 9.