 India needs to worry about terror groups attacking critical infrastructure such as power plants, telecom and banking systems, says Eugene Kaspersky, founder of the world’s biggest private cybersecurity firm. Is India particularly vulnerable or a target for cyberattacks, especially from adversarial neighbours such as China and Pakistan? India is one of the most important countries from a cybersecurity aspect because of its large population, Internet literacy, and as a growing economy. I hope and believe we will never have an inter-state cyberwar, simply because all nations are equally vulnerable. Cyberweapons are like a nuclear weapon now, a deterrent. But I am worried about cyberterrorism. There are many groups that are responsible to no one and they are the worst case scenario for us.
India needs to worry about terror groups attacking critical infrastructure such as power plants, telecom and banking systems, says Eugene Kaspersky, founder of the world’s biggest private cybersecurity firm. Is India particularly vulnerable or a target for cyberattacks, especially from adversarial neighbours such as China and Pakistan? India is one of the most important countries from a cybersecurity aspect because of its large population, Internet literacy, and as a growing economy. I hope and believe we will never have an inter-state cyberwar, simply because all nations are equally vulnerable. Cyberweapons are like a nuclear weapon now, a deterrent. But I am worried about cyberterrorism. There are many groups that are responsible to no one and they are the worst case scenario for us.21 December 2017
India should secure infrastructure against cyber threats, says Kaspersky Labs founder
 India needs to worry about terror groups attacking critical infrastructure such as power plants, telecom and banking systems, says Eugene Kaspersky, founder of the world’s biggest private cybersecurity firm. Is India particularly vulnerable or a target for cyberattacks, especially from adversarial neighbours such as China and Pakistan? India is one of the most important countries from a cybersecurity aspect because of its large population, Internet literacy, and as a growing economy. I hope and believe we will never have an inter-state cyberwar, simply because all nations are equally vulnerable. Cyberweapons are like a nuclear weapon now, a deterrent. But I am worried about cyberterrorism. There are many groups that are responsible to no one and they are the worst case scenario for us.
India needs to worry about terror groups attacking critical infrastructure such as power plants, telecom and banking systems, says Eugene Kaspersky, founder of the world’s biggest private cybersecurity firm. Is India particularly vulnerable or a target for cyberattacks, especially from adversarial neighbours such as China and Pakistan? India is one of the most important countries from a cybersecurity aspect because of its large population, Internet literacy, and as a growing economy. I hope and believe we will never have an inter-state cyberwar, simply because all nations are equally vulnerable. Cyberweapons are like a nuclear weapon now, a deterrent. But I am worried about cyberterrorism. There are many groups that are responsible to no one and they are the worst case scenario for us.Dark Web NightmaresWeak in attack and defence, India walks blind down an unseen war
ARUSHI BEDI
 Think national security and the first thing that comes to mind is the soldier sitting at the border, arms in hand, firing shell after shell to protect his sovereign country come what may. The images might be largely correct, but then long gone are the days of mechanised warfare fought on land with guns and tanks alone. Armed forces throughout the world are now equipping themselves to fight a new kind of unseen war. These are ones fought behind computer screens, but those that have the ability to disrupt countries in ways that don’t just lead to bloodshed of a few at the border. They can trigger mass shutdowns, affecting the lives of common people in ways unimaginable a decade ago.
Think national security and the first thing that comes to mind is the soldier sitting at the border, arms in hand, firing shell after shell to protect his sovereign country come what may. The images might be largely correct, but then long gone are the days of mechanised warfare fought on land with guns and tanks alone. Armed forces throughout the world are now equipping themselves to fight a new kind of unseen war. These are ones fought behind computer screens, but those that have the ability to disrupt countries in ways that don’t just lead to bloodshed of a few at the border. They can trigger mass shutdowns, affecting the lives of common people in ways unimaginable a decade ago.IRAN’S CYBER WARFARE PROGRAM IS NOW A MAJOR THREAT TO THE UNITED STATES
BY DOROTHY DENNING
 Iran is one of the leading cyberspace adversaries of the United States. It emerged as a cyber threat a few years later than Russia and China and has so far demonstrated less skill. Nevertheless, it has conducted several highly damaging cyberattacks and become a major threat that will only get worse.But unlike these other countries, Iran openly encourages its hackers to launch cyberattacks against its enemies.The government not only recruits hackers into its cyber forces but supports their independent operations.
Iran is one of the leading cyberspace adversaries of the United States. It emerged as a cyber threat a few years later than Russia and China and has so far demonstrated less skill. Nevertheless, it has conducted several highly damaging cyberattacks and become a major threat that will only get worse.But unlike these other countries, Iran openly encourages its hackers to launch cyberattacks against its enemies.The government not only recruits hackers into its cyber forces but supports their independent operations.Infographic Of The Day: Inventions That Were Discovered By Accident
NIST’s lead cryptographer talks encryption’s paradigm shifts
By: Brad D. Williams
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/4TS72RBW3BGCPDOBBRCQA645QU.jpg) Cryptography has long attracted research into novel applications for secret messages between parties. For nearly 4,000 years, cryptographic methods have slowly advanced, with notable contributions from many ancient civilizations and modern nations. Since the advent of the internet age, cryptographic applications have rapidly expanded. The ongoing evolution has continued this year, with recent breakthroughs that some experts say could fundamentally transform one of the oldest subfields of contemporary cybersecurity.
Cryptography has long attracted research into novel applications for secret messages between parties. For nearly 4,000 years, cryptographic methods have slowly advanced, with notable contributions from many ancient civilizations and modern nations. Since the advent of the internet age, cryptographic applications have rapidly expanded. The ongoing evolution has continued this year, with recent breakthroughs that some experts say could fundamentally transform one of the oldest subfields of contemporary cybersecurity.The End of Net Neutrality: Implications for National Security
LEVI MAXEY
 The Federal Communications Commission (FCC) voted 3-2 on Thursday to dismantle their authorities to enforce net neutrality rules that prohibit internet service providers, such as Verizon, AT&T, and Comcast, from interfering in the traffic streams that take place over their infrastructure. The reversal of the FCC’s 2015 decision means the federal government will no longer be able to regulate ISPs as if they were a utility, allowing ISPs to privilege some traffic over others and perhaps even throttle or block content they independently decide to – such as controversial political opinions.
The Federal Communications Commission (FCC) voted 3-2 on Thursday to dismantle their authorities to enforce net neutrality rules that prohibit internet service providers, such as Verizon, AT&T, and Comcast, from interfering in the traffic streams that take place over their infrastructure. The reversal of the FCC’s 2015 decision means the federal government will no longer be able to regulate ISPs as if they were a utility, allowing ISPs to privilege some traffic over others and perhaps even throttle or block content they independently decide to – such as controversial political opinions. The Strategic Implications of Non-State #WarBots
By Mark Jacobsen
This essay is part of the #WarBots series, which asked a group of academics and national security professionals to provide their thoughts on the confluence of automation and unmanned technologies and their impact in the conduct of war. We hope this launches a debate that may one day shape policy. Over the past year, a primitive type of WarBot has become a formidable battlefield weapon: the small unmanned aerial system. The threat materialized in October 2016 when a drone booby-trapped by the Islamic State killed two Kurdish soldiers. Within a few months, the Islamic State was flying tens of aerial bombardment missions each day, displayed the capability to drop grenades down the hatches of tanks, and reportedly flew up to a dozen aircraft at a time. The threat was so severe that the Mosul offensive nearly stalled.
INVISIBLE DOOMSDAY MACHINES: THE CHALLENGE OF CLANDESTINE CAPABILITIES AND DETERRENCE
Brendan Rittenhouse Green and Austin Long
Stanley Kubrick’s iconic black comedy Dr. Strangelove remains one of the most insightful works on deterrence. The film revolves around the Doomsday Machine, which will automatically destroy all life on earth if the United States ever launches a nuclear attack on the Soviet Union. After a rogue American general does precisely that, the Soviet ambassador reveals the machine’s existence and explains what is about to happen. American General Buck Turgidson is skeptical, claiming the machine is “an obvious commie trick, Mr. President!” The titular Dr. Strangelove subsequently delivers the film’s biting satirical punch line: “The … whole point of the Doomsday Machine … is lost … if you keep it a secret! Why didn’t you tell the world, eh?”
Impact of Sequestration and the Drawdown on the Different Sectors of the Industrial Base
The United States has long recognized the importance of supporting and sustaining an advanced defense industrial base for maintaining global technological superiority. However, the implementation of the 2011 Budget Control Act's (BCA) enforced reductions to the federal budget has prompted Congressional, DOD, government oversight, and industry officials all to express concerns over the health and future of the defense industrial base. The empirical data presented in this report show that the effect of the defense drawdown on industry was substantial; and that defense contract obligations fell across all platform portfolios (planes, land vehicles, ships, etc.). However, the impact of the drawdown on the different sectors of the defense industrial base varied widely and the varying consequences are discussed herein.
DOWNLOAD THE REPORT
20 December 2017
THE TIES THAT BIND: FAMILIES, CLANS, AND HIZBALLAH’S MILITARY EFFECTIVENESS
MICHAEL EISENSTADT AND KENDALL BIANCHI
 A recent article in a pro-Hizballah media site tells the “Story of Two Martyrs,” Ibrahim and Ahmad Shihab, cousins who grew up together in the town of Baraachit in southern Lebanon. The two were close and went on “jihad” together in June 2016, fighting in the “same trench” in Syria. They were killed in action shortly thereafter, along with another lifelong friend from their hometown who was also a member of the extended Shihab clan. The story of the two cousins and their friendship sheds light on the workings of organizations like Hizballah, which has morphed from a shadowy underground resistance movement and communal militia into a large, quasi-regular military force. In many cases, members belong to the same family or clan, or are close friends. Indeed, this is true of many local and foreign militias that have participated in Syria’s civil war. These social solidarities may contribute to the effectiveness of these militias, as well as organizations like Hizballah, whose institutional DNA still bears the imprint of its militia origins.
A recent article in a pro-Hizballah media site tells the “Story of Two Martyrs,” Ibrahim and Ahmad Shihab, cousins who grew up together in the town of Baraachit in southern Lebanon. The two were close and went on “jihad” together in June 2016, fighting in the “same trench” in Syria. They were killed in action shortly thereafter, along with another lifelong friend from their hometown who was also a member of the extended Shihab clan. The story of the two cousins and their friendship sheds light on the workings of organizations like Hizballah, which has morphed from a shadowy underground resistance movement and communal militia into a large, quasi-regular military force. In many cases, members belong to the same family or clan, or are close friends. Indeed, this is true of many local and foreign militias that have participated in Syria’s civil war. These social solidarities may contribute to the effectiveness of these militias, as well as organizations like Hizballah, whose institutional DNA still bears the imprint of its militia origins.Opium Trade Not Only Funding the Taliban, But Also a Big Contributor to Growing Violence and Corruption in Afghanistan
The additional American ground forces sent to Afghanistan this year are concentrating on Taliban logistics and that means attacks on the drug gang infrastructure. There are thirteen drug gangs in Afghanistan and most rely on Helmand for something. Most of these gangs have a major part of their heroin production in Helmand and all depend on the Helmand access to Pakistan where the military has sufficient authority to make sure chemicals and lab equipment (required to turn the bulky opium into the more compact and much more valuable heroin) get across the border and into Helmand. Half of the opium and heroin leaves the country via Pakistan. Helmand is the key to drug gang operations and the bulk of Taliban income.
Religious extremism poses threat to ASEAN's growth
GWEN ROBINSON, Chief editor, and SIMON ROUGHNEEN
 YANGON/JAKARTA -- With Mt. Agung billowing volcanic ash into the sky above his home in Bali, Khairy Susanto was unsure if he could fly back after joining tens of thousands of fellow Indonesian Islamists at a rally near the presidential palace in Jakarta."Inshallah, we can fly, but it doesn't matter, we will be OK," Susanto said. "We are happy to be here today to celebrate our victory."
YANGON/JAKARTA -- With Mt. Agung billowing volcanic ash into the sky above his home in Bali, Khairy Susanto was unsure if he could fly back after joining tens of thousands of fellow Indonesian Islamists at a rally near the presidential palace in Jakarta."Inshallah, we can fly, but it doesn't matter, we will be OK," Susanto said. "We are happy to be here today to celebrate our victory."Trump National Security Strategy Sees U.S. Confronting China and Russia
By DAVID E. SANGER and MARK LANDLER
 WASHINGTON — President Trump’s first national security strategy envisions a world in which the United States confronts two “revisionist” powers — China and Russia — that are seeking to change the global status quo, often to the detriment of America’s interests. But while the document outlines a detailed plan to push back against China’s global economic ambitions, it says little about dealing with the kind of cyber and information warfare techniques that Moscow used to try to influence the 2016 presidential election.
WASHINGTON — President Trump’s first national security strategy envisions a world in which the United States confronts two “revisionist” powers — China and Russia — that are seeking to change the global status quo, often to the detriment of America’s interests. But while the document outlines a detailed plan to push back against China’s global economic ambitions, it says little about dealing with the kind of cyber and information warfare techniques that Moscow used to try to influence the 2016 presidential election.Three things to know about China’s military strategy
Oriana Skylar
With respect to China policy, the Trump administration has been focused on the North Korean nuclear issue. The Trump administration has pursued a strategy of maximum pressure on North Korea, including declaring North Korea a state sponsor of terrorism and enacting biting sanctions. Earlier this year, the US imposed sanctions on two Chinese individuals as well as the Dalian Global Unity Shipping company and the Bank of Dandong. In September, the Treasury Department added eight North Korean banks and 26 individuals to its list of sanctions, with the majority of the individuals listed residing in China. Most recently on November 21, the Trump administration announced further sanctions, targeting one individual, 30 companies, and 20 vessels that had engaged in trade with North Korea.
Liberated Raqqa The Stench of Death amid Hopes for Life
 The former Islamic State stronghold of Raqqa has been liberated, yet the city remains largely uninhabitable, criss-crossed with mines and strewn with rotting corpses. One man has made it his mission to bring the city back to life.
The former Islamic State stronghold of Raqqa has been liberated, yet the city remains largely uninhabitable, criss-crossed with mines and strewn with rotting corpses. One man has made it his mission to bring the city back to life.
On Dalla Square, where uniformed teens sit around a chipboard fire at the first checkpoint into the city, Abdullah al-Arian notices that the smell is still there. The smell of the "caliphate." The smell of the military offensive. The smell of death.
When the 'Arab Street' Comes to Sweden
Noah Feldman
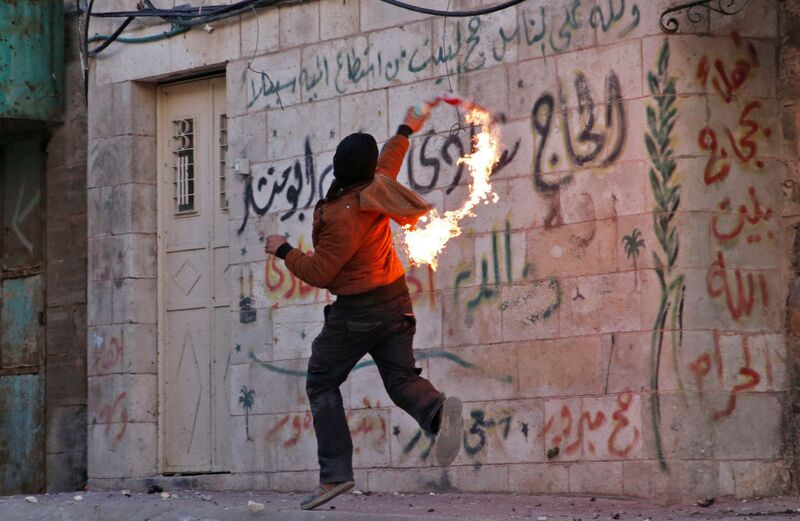 It’s no surprise that U.S. President Donald Trump’s decision to recognize Jerusalem as Israel’s capital has sparked violence in the West Bank and Beirut, or even protests in far-flung Indonesia, which is majority Muslim. But Sweden? Yet the western Swedish city of Gothenburg, headquarters of Volvo Car AB, saw the firebombing of a synagogue on Friday. The same evening, demonstrators in Malmö, in Sweden’s far south, called for their own “intifada” and threatened to shoot Jews.
It’s no surprise that U.S. President Donald Trump’s decision to recognize Jerusalem as Israel’s capital has sparked violence in the West Bank and Beirut, or even protests in far-flung Indonesia, which is majority Muslim. But Sweden? Yet the western Swedish city of Gothenburg, headquarters of Volvo Car AB, saw the firebombing of a synagogue on Friday. The same evening, demonstrators in Malmö, in Sweden’s far south, called for their own “intifada” and threatened to shoot Jews.The Pentagon’s Third Offset May Be Dead, But No One Knows What Comes Next
BY PAUL MCLEARY
 In 2012, the Pentagon’s senior leadership secretly established a new office to work on state-of-the-art weapons. For the next four years, officials there labored away quietly on projects ranging from swarming microdrones to hypervelocity projectiles, until the Pentagon finally revealed the organization’s existence.
In 2012, the Pentagon’s senior leadership secretly established a new office to work on state-of-the-art weapons. For the next four years, officials there labored away quietly on projects ranging from swarming microdrones to hypervelocity projectiles, until the Pentagon finally revealed the organization’s existence.
This shadowy division, called the Strategic Capabilities Office, or SCO, formed part of a larger military strategy to advance technology, known as the Third Offset.
Putting lifelong learning on the CEO agenda
By Amy Edmondson and Bror Saxberg
In an open letter to business leaders, a Harvard Business School professor and a learning engineer at the Chan Zuckerberg Initiative present an emphatic case to make learning a corporate priority. If you are anything like most corporate leaders we know, you say (and mean) the right things when it comes to learning, such as “Our people are our most valuable asset, and their development is a top priority.” But if you are honest with yourself, you also know that your actions often emphasize financial over human capital, and you may leave it to individuals to find the learning opportunities they need. That worked, sort of, when people spent most of their time “doing” rather than “thinking,” “creating,” or “deciding.”
National security strategy plan paints China, Russia as U.S. competitors
Anne Gearan
A new U.S. national security strategy plan presents China and Russia as competitors that want to realign global power in their interests, potentially threatening the United States, Trump administration officials said Sunday. President Trump will present the strategy, a kind of mission statement that guides policymaking, in a speech Monday. Its broad outlines follow his “America First” doctrine of national sovereignty and putting a priority on the economic implications of global engagement. Officials said its main tenets are already in practice.
The Return of Global Russia: An Analytical Framework
PAUL STRONSKI, RICHARD SOKOLSKY
Summary: Russia has employed a range of policy tools in recent years to undermine elements of the U.S.-led international order and expand Moscow’s influence on the global stage.
Since 2012, Russia has been conducting a sophisticated, well-resourced, and, thus far, successful campaign to expand its global influence at the expense of the United States and other Western countries. Moscow has pursued a host of objectives, such as tarnishing democracy and undermining the U.S.-led liberal international order, especially in places of traditional U.S. influence; dividing Western political and security institutions; demonstrating Russia’s return as a global superpower; bolstering Vladimir Putin’s domestic legitimacy; and promoting Russian commercial, military, and energy interests.
Dire warning: U.S. military ‘poorly structured,’ vulnerable to China, Russia threats
By Bill Gertz
 A new study by the Rand Corp. is warning that U.S. military forces are poorly structured to meet the threats posed by China, Russia and other states, as well as the continuing war against Islamic terrorism. The study, “U.S. Military Capabilities and Forces for a Dangerous World,” presents the stark conclusion that the American military needs to reform its structure and war fighting plans to better deal with military challenges. “Put more starkly, assessments in this report will show that U.S. forces could, under plausible assumptions, lose the next war they are called upon to fight, despite the United States outspending China on military forces by a ratio of 2.7 to 1 and Russia by 6 to 1,” the report said. “The nation needs to do better than this.”
A new study by the Rand Corp. is warning that U.S. military forces are poorly structured to meet the threats posed by China, Russia and other states, as well as the continuing war against Islamic terrorism. The study, “U.S. Military Capabilities and Forces for a Dangerous World,” presents the stark conclusion that the American military needs to reform its structure and war fighting plans to better deal with military challenges. “Put more starkly, assessments in this report will show that U.S. forces could, under plausible assumptions, lose the next war they are called upon to fight, despite the United States outspending China on military forces by a ratio of 2.7 to 1 and Russia by 6 to 1,” the report said. “The nation needs to do better than this.”NUKE YOUR DARLINGS: ON WRITING IN NATIONAL SECURITY
VAN JACKSON
 Editor’s Note: Have you ever wondered what writing a book in the national security field entailed? What authors go through, and how they approach a massive writing project? Today marks a new kind of series at War on the Rocks. Cambridge University Press has commissioned Van Jackson, a WOTR senior editor, to write a general interest book about the causes, consequences and risks of the ongoing nuclear standoff on the Korean Peninsula. The catch: He has only six months to complete the 80,000-word manuscript, from scratch. In this unique series, Van will document the daily rhythm of his writing process and progress — highs, lows, pitfalls, distractions, and what works for him.
Editor’s Note: Have you ever wondered what writing a book in the national security field entailed? What authors go through, and how they approach a massive writing project? Today marks a new kind of series at War on the Rocks. Cambridge University Press has commissioned Van Jackson, a WOTR senior editor, to write a general interest book about the causes, consequences and risks of the ongoing nuclear standoff on the Korean Peninsula. The catch: He has only six months to complete the 80,000-word manuscript, from scratch. In this unique series, Van will document the daily rhythm of his writing process and progress — highs, lows, pitfalls, distractions, and what works for him.Will Ukraine Be Hit by Yet Another Holiday Power-Grid Hack?
BY ALYZA SEBENIUS
 The holiday season has not been a joyful time with respect to Ukraine’s power grid. Days before Christmas in 2015, remote hackers wrested control from Ukrainian grid operators, and, by digitally commandeering substations, shut off power for 225,000 customers for several hours. Then, in mid-December of last year, hackers developed a malicious code that, without any real-time human support, disrupted a Kiev transmission station and caused a substantial blackout that lasted roughly an hour in the capital—in the first fully automated grid attack ever seen.
The holiday season has not been a joyful time with respect to Ukraine’s power grid. Days before Christmas in 2015, remote hackers wrested control from Ukrainian grid operators, and, by digitally commandeering substations, shut off power for 225,000 customers for several hours. Then, in mid-December of last year, hackers developed a malicious code that, without any real-time human support, disrupted a Kiev transmission station and caused a substantial blackout that lasted roughly an hour in the capital—in the first fully automated grid attack ever seen.The Pentagon Is Secretly Engaging in ‘Mission Creep’ in Syria
Paul R. Pillar
The other day we learned [3] that there are four times more U.S. troops in Syria than any earlier official figure had acknowledged. The discrepancy did not get much public attention, perhaps because the numbers are small compared to some other U.S. military deployments: about 2,000 troops in Syria, with the earlier official figure being 500. The incomplete count evidently had omitted personnel on short-term assignments and some others performing sensitive missions. A Pentagon spokesman said that release of the newer, more complete figure is part of an effort by Secretary of Defense James Mattis to be more transparent.
Hackers halt plant operations in watershed cyber attack
Hackers halt plant operations in watershed cyber attack
Hackers likely working for a nation-state recently invaded the safety system of a critical infrastructure facility in a watershed attack that halted plant operations, according to cyber investigators and the firm whose software was targeted. FireEye Inc (FEYE.O) disclosed the incident on Thursday, saying it targeted Triconex industrial safety technology from Schneider Electric SE (SCHN.PA). Schneider confirmed that the incident had occurred and that it had issued a security alert to users of Triconex, which cyber experts said is widely used in the energy industry, including at nuclear facilities, and oil and gas plants.
Stopping Company Secrets From Walking Out The Front Door
STRATFOR
 As threats of computer intrusions proliferate, many companies have rightly focused their efforts on fending them off. But few train their staffs on how to spot or respond to other techniques used to steal company secrets, including those exploited by employees with inside access. This topic came up during a recent discussion that my old friend and Stratfor colleague Fred Burton and I participated in for a webinar produced for Stratfor's Threat Lens site called "Beyond the Cyber Espionage Threat." In the course of our presentation, we noted how employees who steal a company's intellectual crown jewels can be driven by a range of motives. While money is often the goal, other factors, including satisfying egos or opposing a company's activity, can push employees to bite the hand that feeds them.
As threats of computer intrusions proliferate, many companies have rightly focused their efforts on fending them off. But few train their staffs on how to spot or respond to other techniques used to steal company secrets, including those exploited by employees with inside access. This topic came up during a recent discussion that my old friend and Stratfor colleague Fred Burton and I participated in for a webinar produced for Stratfor's Threat Lens site called "Beyond the Cyber Espionage Threat." In the course of our presentation, we noted how employees who steal a company's intellectual crown jewels can be driven by a range of motives. While money is often the goal, other factors, including satisfying egos or opposing a company's activity, can push employees to bite the hand that feeds them.THE FCC JUST KILLED NET NEUTRALITY. NOW WHAT?
 Most immediately, the activity will move to the courts, where the advocacy group Free Press, and probably others, will challenge the FCC’s decision. The most likely argument: that the commission’s decision violates federal laws barring agencies from crafting “arbitrary and capricious” regulations. After all, the FCC’s net neutrality rules were just passed in 2015. Activists and many members of Congress, including at least six Republicans, pushed for a delay in the vote, but apart from a brief delay due to a security issue, the vote occurred as planned.
Most immediately, the activity will move to the courts, where the advocacy group Free Press, and probably others, will challenge the FCC’s decision. The most likely argument: that the commission’s decision violates federal laws barring agencies from crafting “arbitrary and capricious” regulations. After all, the FCC’s net neutrality rules were just passed in 2015. Activists and many members of Congress, including at least six Republicans, pushed for a delay in the vote, but apart from a brief delay due to a security issue, the vote occurred as planned.A goal realized: Network lobbyists’ sweeping capture of their regulator
Tom Wheeler
When the Federal Communications Commission (FCC) voted December 14 to repeal the rules protecting a fast, fair, and open internet, the lobbyists for the internet service providers realized their long-envisioned strategy to gut the authority of the agency that since 1934 has been charged with overseeing the activities of the nation’s essential networks.
“Here’s how the telecom industry plans to defang their regulators,” a September 12, 2013 Washington Post headline announced. “[T]elecom giants including Verizon, AT&T and Comcast have launched multiple efforts to shift regulation of their broadband business to other agencies that don’t have nearly as much power as the FCC,” the article explained.
Cyber, EW, signals and space mean realigning the Army’s force structure
By: Mark Pomerleau
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/G262ANSACFD7HNTNAPOXIJNLO4.jpg) The Army is undertaking several initiatives to reorganize itself to integrate emerging technologies, capabilities and concepts within formations and maneuver units. The first is the introduction of cyber and electromagnetic activities (CEMA) cells within all operational units. Over the summer, Maj. Gen. John Morrison, commander of the Cyber Center of Excellence, explained that the service is looking to insert CEMA cells into operational formations.
The Army is undertaking several initiatives to reorganize itself to integrate emerging technologies, capabilities and concepts within formations and maneuver units. The first is the introduction of cyber and electromagnetic activities (CEMA) cells within all operational units. Over the summer, Maj. Gen. John Morrison, commander of the Cyber Center of Excellence, explained that the service is looking to insert CEMA cells into operational formations.Why digital transformation is now on the CEO’s shoulders
By Thomas M. Siebel
Big data, the Internet of Things, and artificial intelligence hold such disruptive power that they have inverted the dynamics of technology leadership. When science and technology meet social and economic systems, you tend to see something akin to what the late Stephen Jay Gould called “punctuated equilibrium” in his description of evolutionary biology. Something that has been stable for a long period is suddenly disrupted radically—and then settles into a new equilibrium.1Analogues across social and economic history include the discovery of fire, the domestication of dogs, the emergence of agricultural techniques, and, in more recent times, the Gutenberg printing press, the Jacquard loom, urban electrification, the automobile, the microprocessor, and the Internet. Each of these innovations collided with a society that had been in a period of relative stasis—followed by massive disruption.
Three Things the US Military Needs to Fight in Europe
BY CAROLINE HOUCK
 For the first time since the Cold War, the U.S. military is relearning what it would take to fight alongside its NATO allies on the European continent, and the soldiers and Marines who took part in the first year of rotational deployments have a few requests. As part of U.S. efforts to reassure European allies and deter Russian aggression, the Army dispatched one of the 10th Mountain Division’s aviation brigades to Europe for nine months, and sent an armored brigade from the 4th Infantry Division to join NATO’s multinational Enhanced Forward Presence battle groups in Poland.
For the first time since the Cold War, the U.S. military is relearning what it would take to fight alongside its NATO allies on the European continent, and the soldiers and Marines who took part in the first year of rotational deployments have a few requests. As part of U.S. efforts to reassure European allies and deter Russian aggression, the Army dispatched one of the 10th Mountain Division’s aviation brigades to Europe for nine months, and sent an armored brigade from the 4th Infantry Division to join NATO’s multinational Enhanced Forward Presence battle groups in Poland.Army eyeing options for long-range electronic attack
By: Amber Corrin
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/3J3XZ774G5B2PD54RNWZJGKBN4.JPG) The Army may not currently have a traditional program of record for long-range electronic attack, but that’s not stopping officials from moving ahead to meet operational needs from the field. Leaders are evaluating different options to meet those needs, including different ways of fielding capabilities in spirals and coordinating with coalition partners that do have such tools already, officials said at an Association of the U.S. Army event held Dec. 13 in Arlington, Virginia.
The Army may not currently have a traditional program of record for long-range electronic attack, but that’s not stopping officials from moving ahead to meet operational needs from the field. Leaders are evaluating different options to meet those needs, including different ways of fielding capabilities in spirals and coordinating with coalition partners that do have such tools already, officials said at an Association of the U.S. Army event held Dec. 13 in Arlington, Virginia.The Army is testing if it wants to operate combat drones remotely
By: Mark Pomerleau
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/X7B5B5XBYFEQXMEY47EKH7RFWI.jpg) The Army hopes to know in early 2019 whether it can operate its large unmanned aircraft system like the Air Force and control drones remotely from hundreds or thousands of miles away. The Air Force’s MQ-1 Predators and MQ-9 Reapers, even when flown halfway around the world, are controlled from a remote location within the United States via satellite link. But the Army’s MQ-1C Gray Eagles — which are division assets used at the tactical and operational levels, and are manufactured by the same company as the Predator and Reaper — are operated locally in theater.
The Army hopes to know in early 2019 whether it can operate its large unmanned aircraft system like the Air Force and control drones remotely from hundreds or thousands of miles away. The Air Force’s MQ-1 Predators and MQ-9 Reapers, even when flown halfway around the world, are controlled from a remote location within the United States via satellite link. But the Army’s MQ-1C Gray Eagles — which are division assets used at the tactical and operational levels, and are manufactured by the same company as the Predator and Reaper — are operated locally in theater.INVISIBLE DOOMSDAY MACHINES: THE CHALLENGE OF CLANDESTINE CAPABILITIES AND DETERRENCE
BRENDAN RITTENHOUSE GREEN AND AUSTIN LONG
 Stanley Kubrick’s iconic black comedy Dr. Strangelove remains one of the most insightful works on deterrence. The film revolves around the Doomsday Machine, which will automatically destroy all life on earth if the United States ever launches a nuclear attack on the Soviet Union. After a rogue American general does precisely that, the Soviet ambassador reveals the machine’s existence and explains what is about to happen. American General Buck Turgidson is skeptical, claiming the machine is “an obvious commie trick, Mr. President!” The titular Dr. Strangelove subsequently delivers the film’s biting satirical punch line: “The … whole point of the Doomsday Machine … is lost … if you keep it a secret! Why didn’t you tell the world, eh?”
Stanley Kubrick’s iconic black comedy Dr. Strangelove remains one of the most insightful works on deterrence. The film revolves around the Doomsday Machine, which will automatically destroy all life on earth if the United States ever launches a nuclear attack on the Soviet Union. After a rogue American general does precisely that, the Soviet ambassador reveals the machine’s existence and explains what is about to happen. American General Buck Turgidson is skeptical, claiming the machine is “an obvious commie trick, Mr. President!” The titular Dr. Strangelove subsequently delivers the film’s biting satirical punch line: “The … whole point of the Doomsday Machine … is lost … if you keep it a secret! Why didn’t you tell the world, eh?”19 December 2017
President Trump's New National Security Strategy
By Anthony H. Cordesman
President Trump's new National Security Strategy (NSS) deserves careful attention, particularly by America's allies and strategic partners and by those who deal with everything the President says or issues in terms of knee jerk criticism. It is a document that President Trump reviewed and altered in some depth and that represents his views—rather than a bureaucratic compromise. At the same time, it both expands on the classic themes of U.S. strategy—rather than rejects them—and commits the U.S. to playing its traditional role in leading the free world.
"America First" Means International, Not Isolation
One of the most critical aspects of the document is its definition of "America first"—one which clearly rejects the isolationism of those who first used the term, and rejects the denial of America's overseas role that some around the President advocated before he appointed his present national security team. It directly addresses both America's need to remain committed overseas and deal with competition from Russia and China:
Subscribe to:
Posts (Atom)