Candace Rondeaux

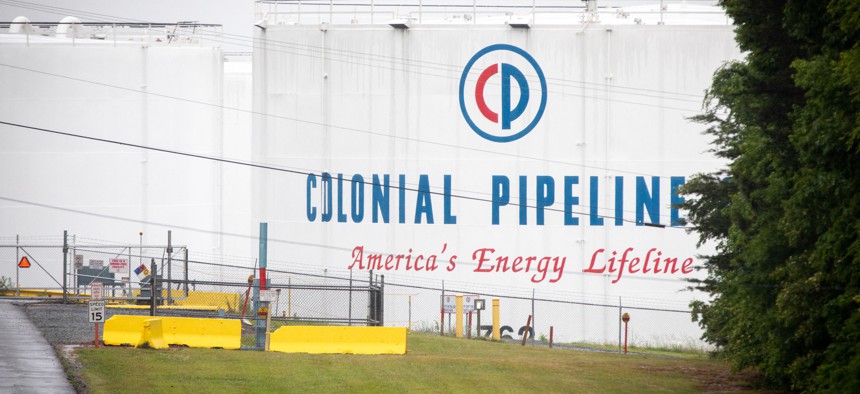
The internet today is on the brink of reaching a state of entropy, as anyone who tried to fill up the gas tank of their car anywhere along the Eastern Seaboard of the United States this week knows. Nearly a week after a crafty network of cybercriminals penetrated the databases of the company that operates the massive Colonial fuel pipeline, which runs nearly the entire length of the East Coast, the United States is still reeling from the crippling cyberattack.
The ransomware attack forced the Colonial Pipeline company to close down a sizable portion of its 5,500-mile-long fuel conduit for days. Only quick action to isolate a server where the ransomware was lodged prevented an even worse catastrophe. Still, the impact was keenly felt and prompted the governors of Virginia, Georgia, Florida and North Carolina to declare a state of emergency over gas shortages after news of the hack drove up consumer anxieties. The online assault on the Colonial Pipeline not only triggered a rush of panic buying at the fuel pump, but also served as another reminder of the dismal state of U.S. cyber defenses—and the even sorrier state of global internet governance. ...












/cloudfront-us-east-1.images.arcpublishing.com/mco/W2SO2Z72FVC4BF7EESBKK4FFDA.jpg)