After the last of the troops leave, the population left behind will be hoping that the West, facing a new conflict in Syria and Iraq, keeps its promises to Afghanistan
Kim Sengupta
PLEASE don't call it our Dien Bien Phu,” Lieutenant Colonel Simon Winkworth, of the Royal Engineers, requested as we gazed out onto a desolate expanse of scrub and sand on which he was going to build Camp Bastion. There were reasons for optimism on that February day, eight years ago, that Britain's Helmand force would not suffer the same fate as the French in Vietnam when a prolonged siege of that base effectively brought their occupation of Vietnam to an end.
The British would not underestimate the enemy as the French had done, we were assured. And John Reid, the then Defence Secretary, stated, when the mission was announced by Tony Blair's government, that it would last no more than two years and end, he hoped, “without a shot being fired” in anger.
End to Britain’s Afghan war
US Marines lower their flag at the handover ceremony. On October 26, the control of the last base was handed over to Afghan forces.
On October 26, 2014, the Union flag was lowered for the last time in Camp Bastion, bringing an end to Britain’s Afghan war after 13 years, three weeks and five days. Although the invasion following 9/11 was in 2001, for the UK the war really started in 2006. Until then, five members of the forces had been killed in total, three from suicide, accidental firearms discharge and a homicide respectively. The death toll today is 453; meanwhile around eight million rounds had been fired in combat; and the financial cost of the mission is over £40bn. The US has supplanted the UK as the main combat force in Helmand over the past few years, and the main handover ceremony to the Afghan army's 215 corps was very much an American and Afghan affair. It was held at Camp Leatherneck, the US camp adjoining Bastion; the speech by Lieutenant-General Joseph Anderson, commander of Regional Command South West made only a passing reference to the UK's contribution in the conflict, focusing instead on those of the Afghan forces and the US Marines.
The senior British officer present, Brigadier Rob Thompson, spoke of the allies helping “Afghanistan get itself back on its feet” and the creation of the “opportunity now for the Afghan leadership to get into the fast lane and move ahead”. He stressed that “we need to get the story into 2014 space and not 2006 space. Don't see Helmand in a lens shaped by 2006. In Lashkar Gar today, you could easily go down the street. I have seen children playing chicken in the street. I have seen policemen at checkpoints.”
In reality all those things could be done and seen in Lashkar Gar, the Helmand capital, in 2006 — before the arrival of the UK task force. At the time, my colleagues and I stayed in a guest house in the city, shopped and drank chai in the bazaar: I accompanied the British commander running a small team, Lieutenant Colonel Henry Worsley, as he went in "soft-skin" Land-Rovers to meet imams and elders in village shuras without body armour and helmets.
The suicide attack
Then came the first suicide attack in Lashkar Gar. The American private security company, DynCorp, had started carrying out poppy eradication in Helmand, and their contractors took to visiting their former colleagues in the US military at the Lashkar Gar base. A car packed with explosives followed them and drove into the main gate.
One of the reasons for making Helmand the location of the UK force, the Government said, was to tackle the poppy harvest: 90 per cent of the heroin on the streets of Britain came from the province, which was responsible for 25 per cent of Afghanistan's opium crop. Sher Mohammed Akhundzada, the governor, was one of the main druglords; the British insisted on his removal, much to President Hamid Karzai's chagrin. Helmand now produces 52 per cent of the Afghan crop. The British military were extremely wary about getting involved in creating another tier of enemy among farmers whose livelihood depended on the crop. As I was leaving Lashkar Gar to fly up to Kabul that February, Lt Col Worsley asked: “Are you going to the British embassy in Kabul? If you are, can you ask them what exactly is the HMG policy on poppy eradication? No one has told us.”
By the summer of 2006, the British had more than poppies to worry about. Helmand was aflame, pitted with lots of mini Dien Bien Phus where small UK units were besieged in their bases by the Taliban.
 Elizabeth Weise
Elizabeth Weise

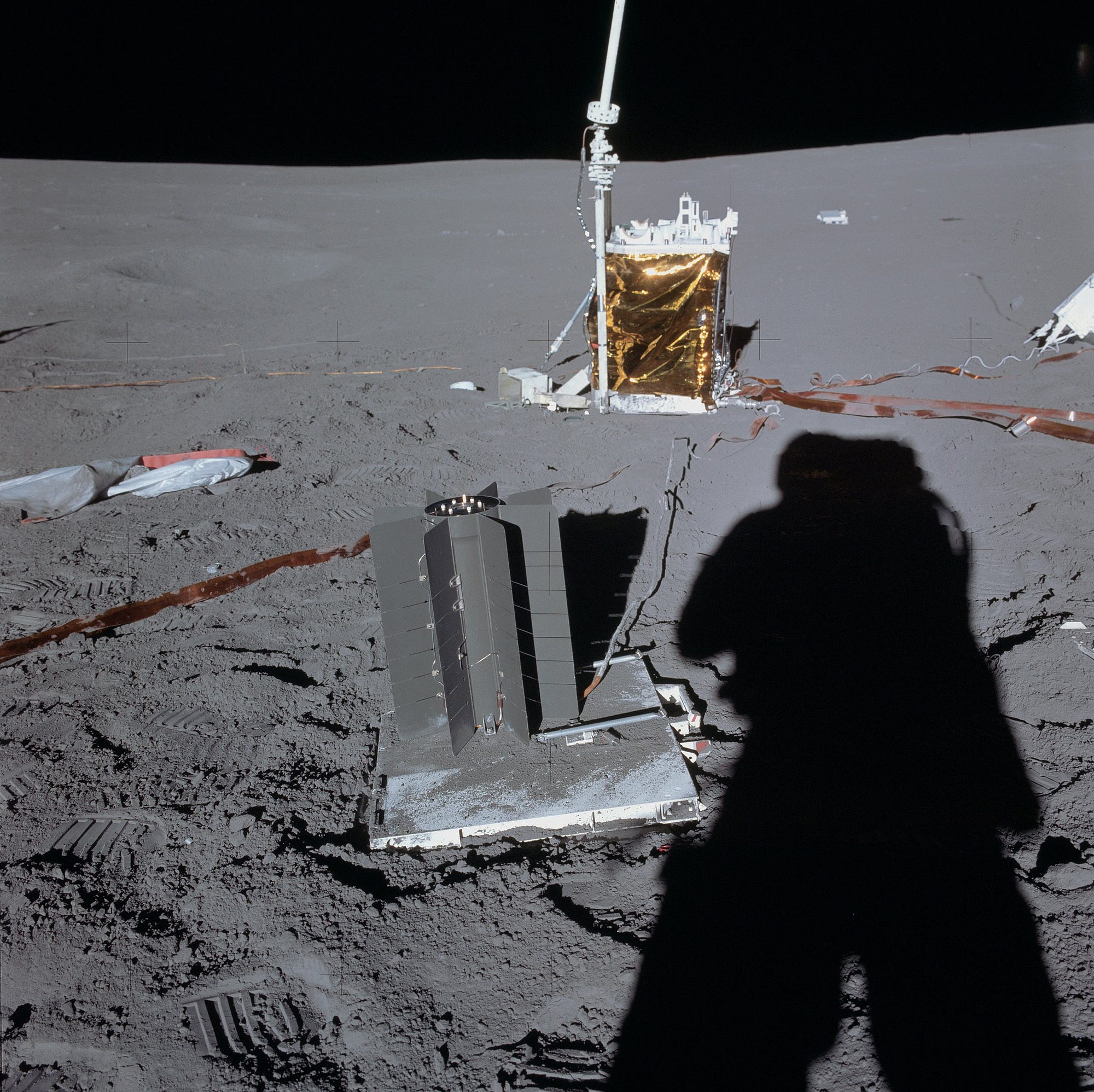 Above—the radioisotope thermoelectric generator from the Apollo 14 mission. NASA photo. At top—a radio check in Afghanistan in March 2014. Army photo
Above—the radioisotope thermoelectric generator from the Apollo 14 mission. NASA photo. At top—a radio check in Afghanistan in March 2014. Army photo