Peter Baker and Eric Schmitt
September 30, 2014
Many Missteps in Assessment of ISIS Threat
WASHINGTON — By late last year, classified American intelligence reports painted an increasingly ominous picture of a growing threat from Sunni extremists in Syria, according to senior intelligence and military officials. Just as worrisome, they said, were reports of deteriorating readiness and morale among troops next door in Iraq.
But the reports, they said, generated little attention in a White House consumed with multiple brush fires and reluctant to be drawn back into Iraq. “Some of us were pushing the reporting, but the White House just didn’t pay attention to it,” said a senior American intelligence official. “They were preoccupied with other crises,” the official added. “This just wasn’t a big priority.”
The White House denies that, but the threat certainly has its attention now as American warplanes pound the extremist group calling itself the Islamic State in hopes of reversing its lightning-swift seizing of territory in Iraq and Syria. Still, even as bombs fall from the sky thousands of miles away, the question of how it failed to anticipate the rise of a militant force that in the space of a few months has redrawn the map of the Middle East resonates inside and outside the Obama administration.
President Obama fueled the debate in an interview broadcast over the weekend when he said that intelligence agencies had underestimated the peril posed by the Islamic State, also known as ISIS or ISIL. Mr. Obama accurately quoted James R. Clapper Jr., the director of national intelligence, acknowledging that he and his analysts did not foresee the stunning success of Islamic State forces or the catastrophic collapse of the Iraqi Army.
But by pointing to the agencies without mentioning any misjudgments of his own, Mr. Obama left intelligence officials bristling about being made into scapegoats and critics complaining that he was trying to avoid responsibility.
“This was not an intelligence community failure, but a failure by policy makers to confront the threat,” said Representative Mike Rogers, Republican of Michigan and chairman of the House Intelligence Committee.
A spokesman denied on Monday that Mr. Obama was blaming intelligence agencies in his interview on “60 Minutes” on CBS News. “That is not what the president’s intent was,” said Josh Earnest, the White House press secretary. “What the president was trying to make clear” was “how difficult it is to predict the will of security forces that are based in another country to fight.”
Mr. Earnest added that “the president’s commander in chief and he’s the one who takes responsibility” for ensuring the national security based on the information provided by intelligence analysts. “And the president continues to have the highest degree of confidence in our intelligence community to continue to provide that advice,” he said.
Caught Off Guard

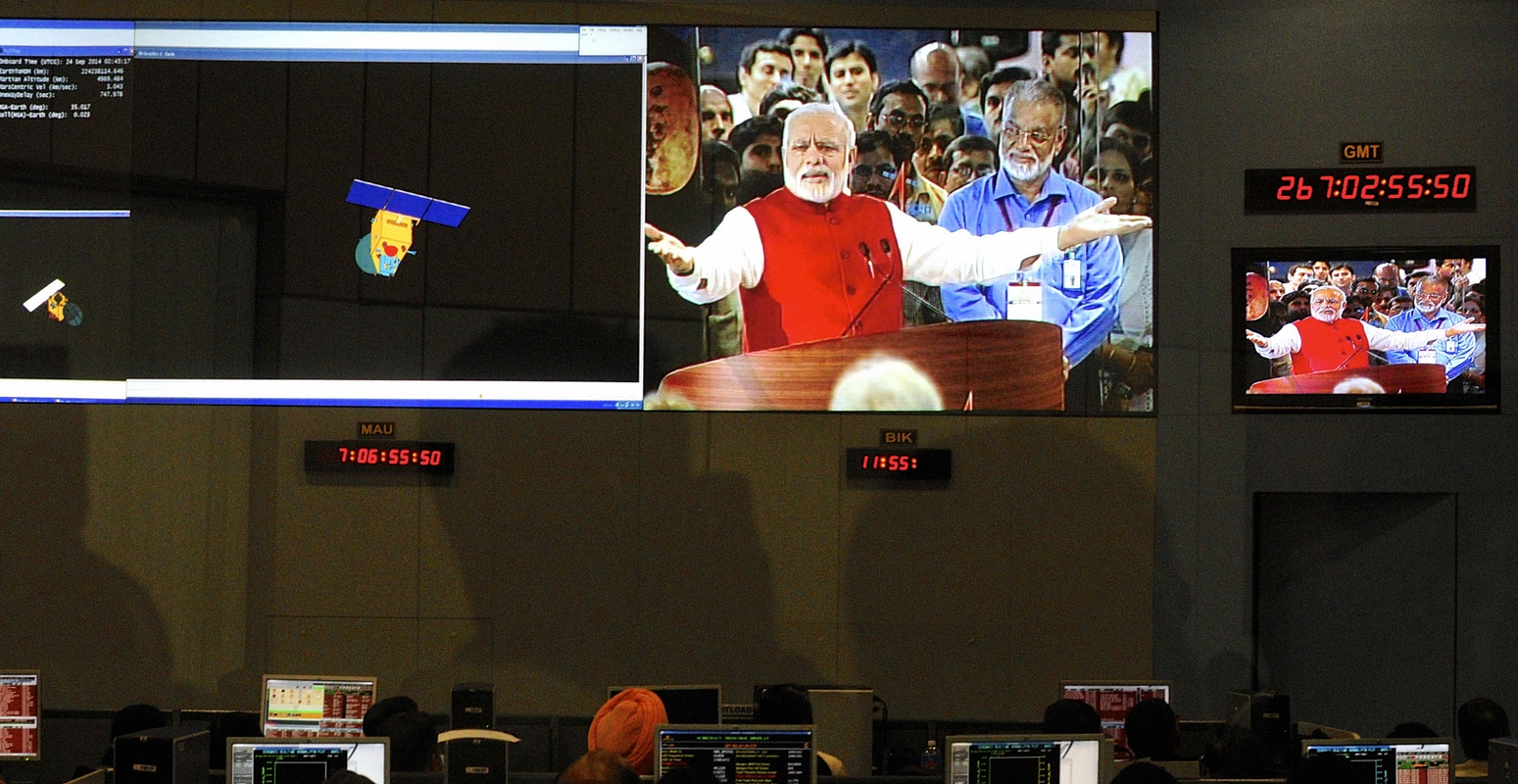 Indian Space Research Organization scientists and engineers watch Prime Minister Narendra Modi (L) on screens after India’s Mars orbiter was successfully put around the Red Planet’s orbit, at their Spacecraft Control Center in the southern Indian city of Bangalore. (Reuters)
Indian Space Research Organization scientists and engineers watch Prime Minister Narendra Modi (L) on screens after India’s Mars orbiter was successfully put around the Red Planet’s orbit, at their Spacecraft Control Center in the southern Indian city of Bangalore. (Reuters)


