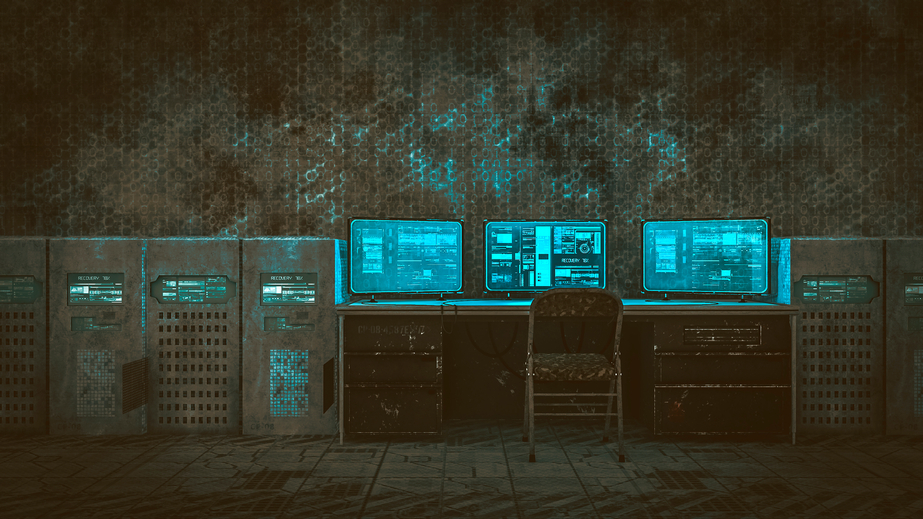
The drafting, negotiation, and passage of the National Defense Authorization Act (NDAA) is an annual event that sets the annual budget for the Department of Defense. During this time Congress is able to exert control over the priorities, guiding principles, and issues that will be addressed by the department in the coming year. The 2018 incarnation of the NDAA, which has just been signed into law by the president, includes, nested in Title XVI, Subtitle C, provisions, a requirement that the White House and the DOD meaningfully investigate, consider, and establish national standards and guidance in the cybersecurity and cyber-warfare space. They must explore the development of a national posture for these issues.
12 January 2018
Cybersecurity Showdown: Why the Military Is Preparing for a New Kind of War
Losing the Information War and How to Win
by Michael Anderson
We are losing the information war. We face an enemy ideology that crafted and shaped an enduring, effective message, near perfecting dissemination and application to relevant target audiences- the disaffected around the globe- while we remain, at best, reactive and, at worst, counter-productive in our own messaging. The extremist ideological message of groups across the Islamic spectrum from Sunni to Shia, Al-Qaeda and affiliates, or ISIL, and other splinter group across the Levant, Maghreb, and the world, are even drawing adherence from developed nations. To secure the proliferation of Western ideals and values of freedom and free-thinking, there must be increased focus on the information war, reshaping the approach to messaging, bringing it on equal or superior footing to the physical efforts across the globe combating the enduring tide of extremist thought infecting the world’s disaffected.
How the (Likely) Next NSA/CyberCom Chief Wants to Enlist AI
BY PATRICK TUCKER
 A look at Lt. Gen. Paul Nakasone’s public statements about artificial intelligence, offense, and defense.
A look at Lt. Gen. Paul Nakasone’s public statements about artificial intelligence, offense, and defense.
The Army general likely to be tapped to head U.S. Cyber Command and the NSA has some big plans for deploying cyber forces and using artificial intelligence in information attacks.
Lt. Gen. Paul Nakasone, who currently leads U.S. Army Cyber Command, is expected to nominated in the next few months to replace Adm. Michael Rogers, as first reported by The Cipher Brief (and confirmed by the Washington Post and a Pentagon source of our own). But caution is in order: the rumor mill says several other contenders are in the running, including Army Lt. Gen. William Mayville. Neither Cyber Command nor the Pentagon would comment about the potential nomination.
The botnet solution everybody already knows about
By: Jessie Bur
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/OITTODFHQVB7RCL6JZXUBKOJ4E.net635972859016060954) Government and industry could help prevent dangerous botnet attacks simply by using tools that already exist, according to a draft report headed to the White House.
Government and industry could help prevent dangerous botnet attacks simply by using tools that already exist, according to a draft report headed to the White House.
Instead, IT officials often ignore those tools because they’re too expensive, too difficult or for other reasons, a recent report from the National Telecommunications and Information Administration said.
“The tools, processes and practices required to significantly enhance the resilience of the internet and communications ecosystem are widely available, if imperfect, and are routinely applied in selected market sectors,” the report said.
Marines Inserting New Technology into Forces
By Yasmin Tadjdeh
 The Marine Corps is looking at ways to insert new technology into its forces earlier in order to prepare for future battles.
The Marine Corps is looking at ways to insert new technology into its forces earlier in order to prepare for future battles.
Key to this effort is experimentation, said Lt. Col. Dan Schmitt, head of the Marine Corps Warfighting Laboratory field testing branch.
Last year, the service introduced a new operating concept called, “How an Expeditionary Force Operates in the 21st Century.” The document — which focused on how Marines will fight in 2025 — put an emphasis on the need for the service to return to its seafaring roots, conduct maneuver warfare and fight as a combined arms force.
The US Military Needs a Teacher Corps to Train Its Partners
BY ELISABETH BRAW
 As we speak, U.S. troops are training Afghan armed forces. U.S.forces were also training them last year, and the year before that. In fact, American troops have been training them ever since the Taliban were toppled in 2001, to the tune of $4 billion per year. Other NATO countries have been training Afghan forces, too. But despite these enormous teaching efforts, the Afghans are nowhere near ready to fight on their own. What we need — and not just in Afghanistan — are dedicated Teacher Corps of didactically talented, well-trained troops.
As we speak, U.S. troops are training Afghan armed forces. U.S.forces were also training them last year, and the year before that. In fact, American troops have been training them ever since the Taliban were toppled in 2001, to the tune of $4 billion per year. Other NATO countries have been training Afghan forces, too. But despite these enormous teaching efforts, the Afghans are nowhere near ready to fight on their own. What we need — and not just in Afghanistan — are dedicated Teacher Corps of didactically talented, well-trained troops.The Only Force That Can Beat Climate Change Is the U.S. Army
BY ANATOL LIEVEN
 The precise extent of human-induced climate change is unclear, but the basic science is unequivocal, as is the danger it poses to the United States. This threat comes from the direct impact of climate change on agricultural production and sea levels but equally importantly from the huge waves of migration that climate change is likely to cause, on a scale that even the world’s richest states and societies will be unable either to prevent or accommodate.
The precise extent of human-induced climate change is unclear, but the basic science is unequivocal, as is the danger it poses to the United States. This threat comes from the direct impact of climate change on agricultural production and sea levels but equally importantly from the huge waves of migration that climate change is likely to cause, on a scale that even the world’s richest states and societies will be unable either to prevent or accommodate.Is the Air Force changing its mind on long-endurance drones?
By: Valerie Insinna
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/NMKTB6PICRFKLCSAYRHFFZS5YM.JPG) WASHINGTON — The U.S. Air Force has been resistant to buy ultrahigh-endurance drones, but a recent $48 million investment in the technology could signify that the service is changing its mind about its requirements, the head of Aurora Flight Sciences said.
WASHINGTON — The U.S. Air Force has been resistant to buy ultrahigh-endurance drones, but a recent $48 million investment in the technology could signify that the service is changing its mind about its requirements, the head of Aurora Flight Sciences said.
On Wednesday, Aurora Flight Sciences announced that the Air Force had awarded it a $48 million contract to create a certified version of its Orion medium altitude, long-endurance unmanned aerial system.
Mobile Devices
To find out which types of devices were most in demand this past holiday season, Flurry Analytics has analyzed new device activations during the week leading up to Christmas.
According to their findings, Apple was the big winner this holiday season. iPhones and iPads accounted for 44 percent of all new device activations between December 19 and 25, with Samsung coming in second at 26 percent of newly activated devices.
Once again, large-screen smartphones, so-called phablets, proved particularly popular under the Christmas tree. They accounted for 53 percent of new device activations this holiday season, up from 37 percent last year and just 27 percent in 2015. Once derided as clunky niche devices, larger phones such as Samsung's Galaxy Note or Apple's iPhone 8 Plus have apparently become the new norm. Let's see if evolution will give us bigger hands to deal with the added screen sizes.
11 January 2018
'US may help India in war against terror'
 'If the US-Pakistan relationship continues to suffer, Pakistan may feel it has less to lose and decide that it need not keep a leash on LeT in order to appease America.' 'A tougher US policy toward Pakistan could lead to an emboldened and strengthened LeT and JeM, resulting in more terrorist attacks in India.' Is the United States serious about withholding military aid worth over $1 billion to Pakistan? Or is this mere sabre-rattling by the Donald J Trump administration, before business returns to usual in the weeks to come?
'If the US-Pakistan relationship continues to suffer, Pakistan may feel it has less to lose and decide that it need not keep a leash on LeT in order to appease America.' 'A tougher US policy toward Pakistan could lead to an emboldened and strengthened LeT and JeM, resulting in more terrorist attacks in India.' Is the United States serious about withholding military aid worth over $1 billion to Pakistan? Or is this mere sabre-rattling by the Donald J Trump administration, before business returns to usual in the weeks to come?India’s jobless growth is not a myth
Mahesh Vyas
Will Pakistan Close NATO’s Supply Routes into Afghanistan?
 ‘I’m not concerned,’ the defense secretary tells reporters after the White House announced an intention to suspend military aid to Islamabad. U.S. Defense Secretary Jim Mattis played down the prospect that Pakistan might close NATO’s supply routes into Afghanistan after the Trump administration said it would suspend military aid to Islamabad. Alliance forces rely on Pakistani roads to haul supplies to landlocked Afghanistan. Pakistan closed them once before, after a 2011 U.S. airstrike killed two dozen of its soldiers. “No, I’m not concerned,” Mattis told reporters on Friday at the Pentagon when asked about the prospect of Pakistan shutting down what the military calls Ground Lines of Communication, or GLOCs.
‘I’m not concerned,’ the defense secretary tells reporters after the White House announced an intention to suspend military aid to Islamabad. U.S. Defense Secretary Jim Mattis played down the prospect that Pakistan might close NATO’s supply routes into Afghanistan after the Trump administration said it would suspend military aid to Islamabad. Alliance forces rely on Pakistani roads to haul supplies to landlocked Afghanistan. Pakistan closed them once before, after a 2011 U.S. airstrike killed two dozen of its soldiers. “No, I’m not concerned,” Mattis told reporters on Friday at the Pentagon when asked about the prospect of Pakistan shutting down what the military calls Ground Lines of Communication, or GLOCs.Pakistan Will Try to Make Trump Pay
 Before the news cycle—and the president himself—got consumed with the new White House tell-all last week, Donald Trump made a good foreign policy decision, albeit seemingly in haste. The administration announced it was suspending security assistance to Pakistan, on the grounds that the country is continuing to arm, assist, fund, and provide sanctuary to a wide array of Islamist militant groups that are murdering U.S. troops and their allies in Afghanistan. Well-placed sources involved with calculating the relevant funds have told me that this was not a planned policy and took the other agencies, not to mention the Pakistanis, by complete surprise. Rather it was an ex post facto response to Trump’s January 1, 2018 tweet vituperatively repining that:
Before the news cycle—and the president himself—got consumed with the new White House tell-all last week, Donald Trump made a good foreign policy decision, albeit seemingly in haste. The administration announced it was suspending security assistance to Pakistan, on the grounds that the country is continuing to arm, assist, fund, and provide sanctuary to a wide array of Islamist militant groups that are murdering U.S. troops and their allies in Afghanistan. Well-placed sources involved with calculating the relevant funds have told me that this was not a planned policy and took the other agencies, not to mention the Pakistanis, by complete surprise. Rather it was an ex post facto response to Trump’s January 1, 2018 tweet vituperatively repining that:Why Pakistan and America Can't Stand Each Other—But Can't Step Away
Mohammed Ayoob
China may build second foreign naval base in Pakistan amid Trump’s row with Islamabad
 China is reportedly planning to boost its military presence overseas with its second foreign naval base in Pakistan. The news comes amid a row between the US and Pakistan, with Washington freezing security funding for Islamabad. After setting up its first foreign naval facility in Djibouti in August of last year, right next to the Pentagon’s base, Beijing may now seek to gain a foothold in Pakistan. China plans to build a second overseas base near Gwadar – a strategically important Pakistani port on the Arabian Sea, according to sources close to the Chinese Army, as cited by the South China Morning Post.
China is reportedly planning to boost its military presence overseas with its second foreign naval base in Pakistan. The news comes amid a row between the US and Pakistan, with Washington freezing security funding for Islamabad. After setting up its first foreign naval facility in Djibouti in August of last year, right next to the Pentagon’s base, Beijing may now seek to gain a foothold in Pakistan. China plans to build a second overseas base near Gwadar – a strategically important Pakistani port on the Arabian Sea, according to sources close to the Chinese Army, as cited by the South China Morning Post.Roads to Nowhere: Asia’s Risky Obsession With Infrastructure
By Ravi Prasad
 There aren’t many words that sum up today’s economic growth paradigm in developing countries better than “infrastructure.” Roads, railways, airports, telecommunications grids, and power stations are being prioritized by governments all around the developing world. From Urumqi to Ulaanbaatar, Bangkok to Baku and beyond, policymakers in developing countries are forming a consensus that infrastructure is the critical ingredient for economic development.
There aren’t many words that sum up today’s economic growth paradigm in developing countries better than “infrastructure.” Roads, railways, airports, telecommunications grids, and power stations are being prioritized by governments all around the developing world. From Urumqi to Ulaanbaatar, Bangkok to Baku and beyond, policymakers in developing countries are forming a consensus that infrastructure is the critical ingredient for economic development.Myanmar's Unhappy Rebels
By Neil Thompson
 With the latest Union Peace Conference (which is held every six months as part of Myanmar’s peace process) coming in late January, Myanmar’s government faces the serious problem that the event would be vulnerable to an offensive by those ethnic armed groups who reject the government’s controversialNational Ceasefire Agreement (NCA) as the basis for a viable national peace agreement.
With the latest Union Peace Conference (which is held every six months as part of Myanmar’s peace process) coming in late January, Myanmar’s government faces the serious problem that the event would be vulnerable to an offensive by those ethnic armed groups who reject the government’s controversialNational Ceasefire Agreement (NCA) as the basis for a viable national peace agreement.Could China spring a nice surprise in 2018?
 After Chinese President Xi Jinping gained near-total political supremacy at the 19th Chinese Communist Party congress in late October, the most pressing question on the minds of China watchers was what he would do with his enormous power. Conventional wisdom now appears to lean toward pessimism. Most analysts think that Beijing will most likely maintain its current course under a powerful leader who has centralized decision-making authority. On the domestic front, Xi is expected to continue to support investment-driven growth while delaying painful financial deleveraging and major structural reforms.
After Chinese President Xi Jinping gained near-total political supremacy at the 19th Chinese Communist Party congress in late October, the most pressing question on the minds of China watchers was what he would do with his enormous power. Conventional wisdom now appears to lean toward pessimism. Most analysts think that Beijing will most likely maintain its current course under a powerful leader who has centralized decision-making authority. On the domestic front, Xi is expected to continue to support investment-driven growth while delaying painful financial deleveraging and major structural reforms.Has Xi Fully Consolidated His Power Over the Military?
By Charlotte Gao
 Recently, multiple signs have shown that Chinese President Xi Jinping, who also holds the positions of chairman of the Central Military Commission (CMC) — the highest body that controls China’s military — and general secretary of the Chinese Communist Party (CCP) Central Committee, has further consolidated his power over Chinese military. On December 27, 2017, the CCP Central Committee announced that the Chinese People’s Armed Police Force (PAP), which had been overseen by both the State Council and the CMC since 1982, would be put under the command of the CMC alone from January 1, 2018.
Recently, multiple signs have shown that Chinese President Xi Jinping, who also holds the positions of chairman of the Central Military Commission (CMC) — the highest body that controls China’s military — and general secretary of the Chinese Communist Party (CCP) Central Committee, has further consolidated his power over Chinese military. On December 27, 2017, the CCP Central Committee announced that the Chinese People’s Armed Police Force (PAP), which had been overseen by both the State Council and the CMC since 1982, would be put under the command of the CMC alone from January 1, 2018.Cyber Vigilantes & Hacktivists: Double-Edged Sword Against ISIS
LEVI MAXEY
 Bottom Line: Cyber vigilantes and “hacktivists” increasingly fill the void left by governments in combating terrorist activity online. While such politically motivated non-state hackers are relatively effective at removing the presence of terrorist content, their continued operations could damage overall counterterrorism efforts by undermining intelligence operations – say by taking down a website that the CIA or NSA is monitoring. By letting these groups run loose – if even for a noble cause – the U.S. risks undermining international norms of cyber operations among states by legitimizing the phenomenon of “patriotic hackers” used as proxies by governments engaging in deniable operations.
Bottom Line: Cyber vigilantes and “hacktivists” increasingly fill the void left by governments in combating terrorist activity online. While such politically motivated non-state hackers are relatively effective at removing the presence of terrorist content, their continued operations could damage overall counterterrorism efforts by undermining intelligence operations – say by taking down a website that the CIA or NSA is monitoring. By letting these groups run loose – if even for a noble cause – the U.S. risks undermining international norms of cyber operations among states by legitimizing the phenomenon of “patriotic hackers” used as proxies by governments engaging in deniable operations.A Spending Spree as a Means of Fulfilling the Saudi Vision
 Saudi Arabia's 2018 budget calls for spending a record amount of money, and based on precedent, actual spending will likely eclipse that figure. About 20 percent of the budget is devoted to military spending, but it also includes a substantial increase in spending on programs benefiting the populace. The careful introduction of new tax measures and a levy on expatriate workers are part of the government's unprecedented push to expand non-oil revenue.
Saudi Arabia's 2018 budget calls for spending a record amount of money, and based on precedent, actual spending will likely eclipse that figure. About 20 percent of the budget is devoted to military spending, but it also includes a substantial increase in spending on programs benefiting the populace. The careful introduction of new tax measures and a levy on expatriate workers are part of the government's unprecedented push to expand non-oil revenue.Ukraine on the brink of kleptocracy
On January 3rd former Georgian President Michael Saakashvili’s plea for asylum in Ukraine was turned down, removing a key obstacle to deport him to Georgia. If deported, he will likely be show-trialled without a fair chance of defence. Since Saakashvili broke his alliance with President Poroshenko, the Ukrainian authorities have been working overtime to get rid of their new political opponent. The Soviet-style harassment campaign started with stripping him of his Ukrainian citizenship (a decision judged illegal by most independent experts), denying him entry into Ukraine, and arbitrary arrests of his aides. Ukrainian Prosecutor General Yuriy Lutsenko tried to bring about his own political show trial of Saakashvili, which he had to abandon on November 13th, formally due to weak evidence, but in effect due to pressure from the EU and the US.
Russian Analytical Digest No 212: Information Warfare
By Jolanta Darczewska, Piotr Zochowski, Robert W. Orttung, Marlene Laruelle and Gemma Pörzgen for Center for Security Studies (CSS)
 The four articles in this edition of the RAD look at 1) how Russia’s contemporary ‘activities’ directed against the West reflect Cold War-ear KGB disinformation operations known as ‘active measures’; 2) the nature of Russia’s intervention in the 2016 US presidential election as well as the impact of Moscow’s on US politics; 3) Russia’s influence in France, particularly when it comes to culture, politics, economics and the media; and 4) the effect of Russian disinformation efforts on Germany’s 2017 federal elections.
The four articles in this edition of the RAD look at 1) how Russia’s contemporary ‘activities’ directed against the West reflect Cold War-ear KGB disinformation operations known as ‘active measures’; 2) the nature of Russia’s intervention in the 2016 US presidential election as well as the impact of Moscow’s on US politics; 3) Russia’s influence in France, particularly when it comes to culture, politics, economics and the media; and 4) the effect of Russian disinformation efforts on Germany’s 2017 federal elections.The Wolfowitz Doctrine
Written by Dan Steinbock
Despite continued nuclear threats, all US postwar presidents have failed to reset relations with Russia. Why? The “New Cold War" between the US and Russia began a decade ago. The elevated tensions in the Korean Peninsula are only a part of the collateral damage around the world. But what led to the new friction? The simple response is the Wolfowitz Doctrine.
How to Break Up Europe’s Axis of Illiberalism
BY SLAWOMIR SIERAKOWSKI
 Western observers tend to conflate Europe’s two leading proponents of right-wing populism: Hungary’s prime minister, Viktor Orban, and the chairman of Poland’s ruling Law and Justice Party, Jaroslaw Kaczynski. Kaczynski has long promised the advent of “Budapest in Warsaw,” an allusion to Orban’s model of “illiberal democracy” that the Hungarian leader unapologetically touted in a 2014 speech. And in 2016, both leaders proudly announced a “cultural counterrevolution” within the European Union.
Western observers tend to conflate Europe’s two leading proponents of right-wing populism: Hungary’s prime minister, Viktor Orban, and the chairman of Poland’s ruling Law and Justice Party, Jaroslaw Kaczynski. Kaczynski has long promised the advent of “Budapest in Warsaw,” an allusion to Orban’s model of “illiberal democracy” that the Hungarian leader unapologetically touted in a 2014 speech. And in 2016, both leaders proudly announced a “cultural counterrevolution” within the European Union.Russia 'simulated full-scale war' against Nato, says military commander
Samuel Osborne
 Russian war games held last September “simulated a large-scale military attack against Nato“, the commander of the Estonian Defence Forces has claimed. Riho Terras confirmed Nato’s fears that the Zapad (or “West”) exercises were used to simulate a conflict with the US-led alliance and show off Russia’s ability to amass large numbers of troops at extremely short notice in the event of a conflict. The drills – which were held in Belarus, the Baltic Sea, western Russia and its Kaliningrad outpost between 14 and 20 September last year – depicted a fictional scenario concerned with attacks by militants, according to Russia’s defence ministry.
Russian war games held last September “simulated a large-scale military attack against Nato“, the commander of the Estonian Defence Forces has claimed. Riho Terras confirmed Nato’s fears that the Zapad (or “West”) exercises were used to simulate a conflict with the US-led alliance and show off Russia’s ability to amass large numbers of troops at extremely short notice in the event of a conflict. The drills – which were held in Belarus, the Baltic Sea, western Russia and its Kaliningrad outpost between 14 and 20 September last year – depicted a fictional scenario concerned with attacks by militants, according to Russia’s defence ministry. An Australian Perspective on Identity, Social Media, and Ideology as Drivers for Violent Extremism
By Kate McNair
Countering Violent Extremism (CVE) is a leading initiative by many western sovereigns to reduce home-grown terrorism and extremism. Social media, ideology, and identity are just some of the issues that fuel violent extremism for various individuals and groups and are thus areas that CVE must be prepared to address. Text: On March 7, 2015, two brothers aged 16 and 17 were arrested after they were suspected of leaving Australia through Sydney Airport to fight for the Islamic State[1]. The young boys fouled their parents and forged school letters. Then they presented themselves to Australian Immigration and Border Protection shortly after purchasing tickets to an unknown middle eastern country with a small amount of funds and claimed to be on their way to visit family for three months. Later, they were arrested for admitting to intending to become foreign fighters for the Islamic State. October 2, 2015, Farhad Khalil Mohammad Jabar, 15 years old, approached Parramatta police station in Sydney’s West, and shot civilian police accountant Curtis Cheng in the back[2]. Later it was discovered that Jabar was inspired and influenced by two older men aged 18 and 22, who manipulated him into becoming a lone wolf attacker, and supplied him the gun he used to kill the civilian worker.
Infographic Of The Day: The Year In News 2017 According To 2.8 Billion Tweets
Expanding the Menu: The Case for CYBERSOC
by Benjamin Brown
Introduction
The United States military should develop cyber special operations capabilities to expand the menu of policy options for addressing threats to U.S. interests and national security. As the roles of the cyber domain in modern conflict expands, new possibilities emerge for special operations to accomplish strategic objectives by employing cyber functions. The creation of Cyber Special Operations Forces (Cyber SOF) within the United States Special Operations Command (SOCOM) would empower the U.S. military to exploit cyber-enabled special operations. Cyber SOF will best enhance U.S. special operations capabilities by taking shape as a sub-unified command within SOCOM. This Cyber Special Operations Command (CYBERSOC) would position Cyber SOF to play supporting or leading roles as a key component of integrated special operations campaigns.
Cross-Domain Network Engagement: Geopolitical Competitors, Cross-domain Considerations and Multi-Domain Battle
by Victor R. Morris
The character of war, strategy development and operational dilemmas change over time, therefore operational approaches must do the same. Joint Countering Threat Networks (JP 3-25) includes versatile lines of effort to identify, neutralize, disrupt or destroy threat networks. These efforts enable engagement of friendly, neutral or unknown actors and mission objectives. To successfully engage networks, more advanced human-machine networks need to be understood and analyzed. For example, battle networks are technologically enhanced Anti-Access Area Denial (A2/AD) and human-machine systems that will influence current and future conflict. This assessment outlines a revised US Army Network Engagement construct to achieve cross-domain effects involving a variety of actors and competitors in a convergent operational environment.
Drone swarm tactics get tryout for infantry to use in urban battlespace
By: Todd South
The Department of Defense successfully tested a drone swarm in 2016. Officials want to put drone swarms in the hands of light infantry. The science fiction-sounding goal: Put an autonomous robot swarm of 250 or more drones under the control of light infantry soldiers or Marines to do complex tasks on the urban battlefield. Competitors are now tackling that goal in a multi-stage event announced late last year by the Defense Advanced Research Projects Agency. Events called Sprinters are intended to develop “offensive swarm-enabled tactics” for these emerging technologies. Swarm drone technology already exists. In 2016, the Defense Department successfully tested micro-drone swarms at China Lake, California. They dropped 103 Perdix drones from three F/A-18 Super Hornet jet fighters.
Next-gen sensors could fit on, and bend like, a Band-Aid
By: Adam Stone
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/U23OXGXIAVBIFAHKGBUW3HZ45M.jpg) Traditionally, intelligence, surveillance and reconnaissance sensors have been hulking antennae and big boxes that often need to be bolted into place. But researchers from Harvard and the Air Force want to shrink those sensors down to the size of a Band-Aid, creating a new world of possibilities and sensor applications. For example, imagine a sensor whose electronic components have been digitally printed into a thin, bendable, stretchable sheet of elastic material. “If you can write those electronics right onto that material, you get the ISR capability without adding any new weight,” said Mike Durstock, Air Force Research Lab (AFRL) branch chief for the soft matters materials branch.
Traditionally, intelligence, surveillance and reconnaissance sensors have been hulking antennae and big boxes that often need to be bolted into place. But researchers from Harvard and the Air Force want to shrink those sensors down to the size of a Band-Aid, creating a new world of possibilities and sensor applications. For example, imagine a sensor whose electronic components have been digitally printed into a thin, bendable, stretchable sheet of elastic material. “If you can write those electronics right onto that material, you get the ISR capability without adding any new weight,” said Mike Durstock, Air Force Research Lab (AFRL) branch chief for the soft matters materials branch.What’s Next for Vietnam’s New Military Peacekeeping Role?
By Prashanth Parameswaran
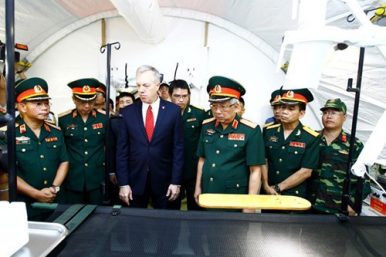 Last week, Vietnam held a ceremony that featured some key developments in the country’s ongoing efforts to boost its involvement in international peacekeeping. Though these developments are part of a broader ongoing transition, they are nonetheless worth noting given the importance that Hanoi has placed on peacekeeping as part of its wider defense and foreign policy in recent years. Though Vietnam’s contribution to UN peacekeeping operations only officially began in 2014, Hanoi has long placed an emphasis on this as part of its contributions to the international community and within its defense relationships with key partners.
Last week, Vietnam held a ceremony that featured some key developments in the country’s ongoing efforts to boost its involvement in international peacekeeping. Though these developments are part of a broader ongoing transition, they are nonetheless worth noting given the importance that Hanoi has placed on peacekeeping as part of its wider defense and foreign policy in recent years. Though Vietnam’s contribution to UN peacekeeping operations only officially began in 2014, Hanoi has long placed an emphasis on this as part of its contributions to the international community and within its defense relationships with key partners.Mattis on War, Tyranny, Revolution and Body Counts
 Defense Secretary Jim Mattis has spent more than 40 years in the study and practice of war, but his extensive thoughts and writings on the subject have often been selectively reduced to chesty one-liners. There's the admonition to the troops: "Be polite, be professional, but have a plan to kill everybody you meet." And another: "There's some a------s in the world that just need to be shot." Other examples of bumper sticker bravado could be cited that tend to drown out the context and Mattis' consistent underlying message in a career as Marine legend and four-star general -- that being prepared for war is the best way to prevent it.
Defense Secretary Jim Mattis has spent more than 40 years in the study and practice of war, but his extensive thoughts and writings on the subject have often been selectively reduced to chesty one-liners. There's the admonition to the troops: "Be polite, be professional, but have a plan to kill everybody you meet." And another: "There's some a------s in the world that just need to be shot." Other examples of bumper sticker bravado could be cited that tend to drown out the context and Mattis' consistent underlying message in a career as Marine legend and four-star general -- that being prepared for war is the best way to prevent it.10 January 2018
Government Mustn’t Be In Denial Over Aadhaar Security; It Is Real, But Largely Fixable
by R Jagannathan
Subscribe to:
Posts (Atom)
