Roger McNamee and Sandy Parakilas
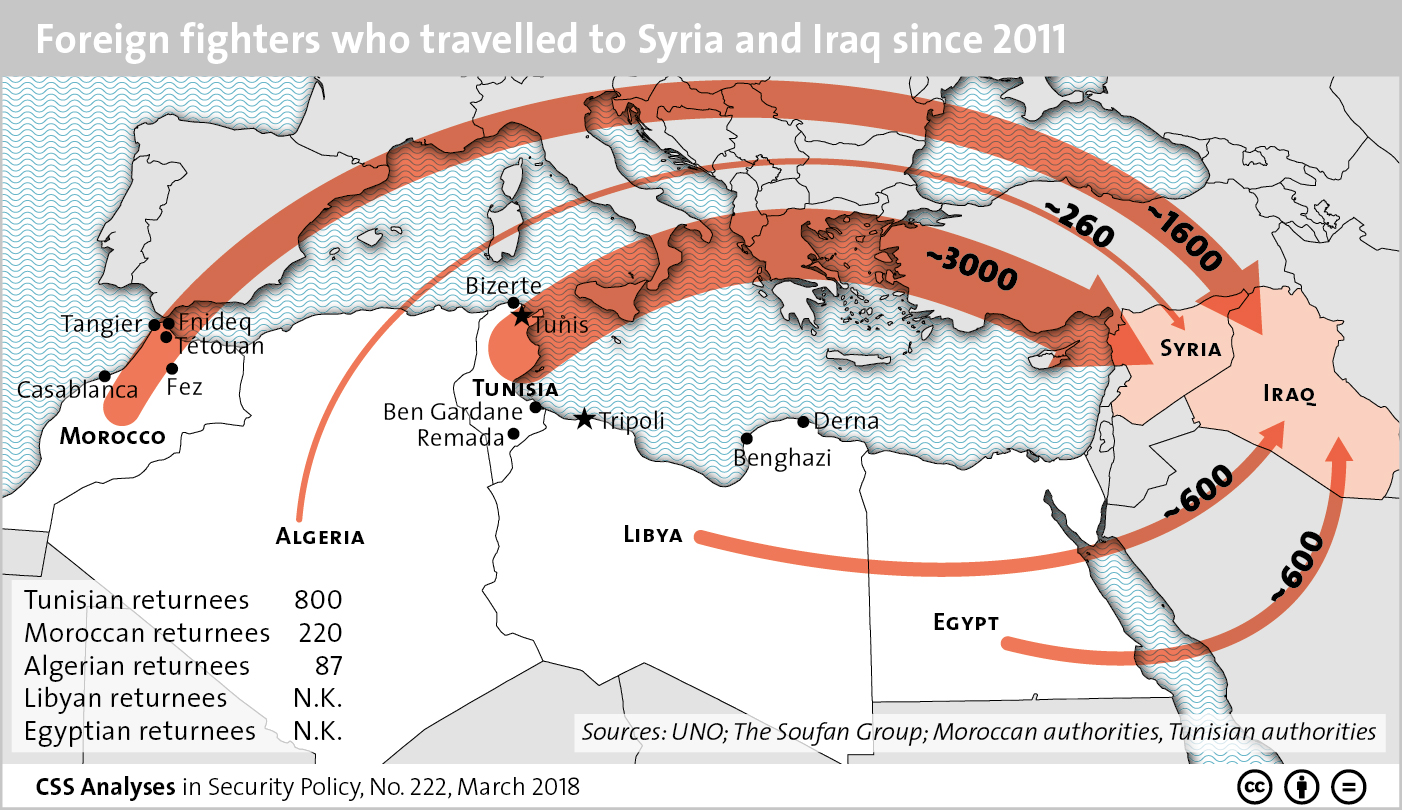
 ‘The big data companies are opaque to consumers and regulators alike, so few people understand the risks and companies can often hide data breaches for a long time.’ The Observer reported on Saturday that Cambridge Analytica acquired 50m Facebook profiles from a researcher in 2014. This appears to have been among the most consequential data breaches in history, with an impact that may rival the breach of financial records from Equifax. There are many problematic aspects to this. It appears the information was harvested by a researcher who collected data not only on the 270,000 or so users who Facebook said took his survey but also on their friends, who knew nothing about the survey, and then passed it to Cambridge Analytica in violation of Facebook’s terms of service. There are questions now over whether the data was destroyed.
‘The big data companies are opaque to consumers and regulators alike, so few people understand the risks and companies can often hide data breaches for a long time.’ The Observer reported on Saturday that Cambridge Analytica acquired 50m Facebook profiles from a researcher in 2014. This appears to have been among the most consequential data breaches in history, with an impact that may rival the breach of financial records from Equifax. There are many problematic aspects to this. It appears the information was harvested by a researcher who collected data not only on the 270,000 or so users who Facebook said took his survey but also on their friends, who knew nothing about the survey, and then passed it to Cambridge Analytica in violation of Facebook’s terms of service. There are questions now over whether the data was destroyed.











/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/KHKO67JAVNFKRLZR5DQWOJ56GQ.jpg)
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/TI4OJD7LH5E5VBSLWAROKNMIAM.jpg)
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/UYN4WMLRIZBSDEGXEP57JLJAEQ.jpg)